Sort by topics
7 Must-Have Certifications to Look for in a Reliable IT Partner
Not all IT partners are created equal. In regulated, high-risk and AI-driven environments, certifications are no longer a “nice to have”. They are hard proof that a software company can deliver securely, responsibly and at scale. For enterprise clients and public institutions, the right certifications often determine whether a vendor is even eligible to participate in strategic projects. Below are seven essential certifications and authorizations that define a mature, enterprise-ready IT partner – including a groundbreaking new standard that is setting the future benchmark for responsible AI development. 1. Why These Certifications Matter When Choosing an IT Partner These certifications are not accidental or aspirational. They represent the most commonly required standards in enterprise tenders, public-sector procurements and regulated IT projects across Europe. Together, they cover the core expectations placed on modern technology partners: information security, quality assurance, service continuity, regulatory compliance, sustainability, workforce safety and, increasingly, responsible artificial intelligence governance. In many large-scale projects, the absence of even one of these certifications can disqualify a vendor at the pre-selection stage. This makes the list not a marketing statement, but a practical reflection of what organizations actually demand when selecting long-term, strategic IT partners. 1.1 ISO/IEC 27001 – Information Security Management System ISO/IEC 27001 defines how an organization identifies, assesses and controls risks related to information security. It focuses specifically on protecting information assets such as client data, intellectual property and critical systems against unauthorized access, loss or disruption. For IT partners, this certification confirms that security is managed as a dedicated discipline – with formal risk assessments, incident response procedures and continuous monitoring. Working with an ISO 27001-certified vendor reduces exposure to data breaches, regulatory penalties and security-driven operational downtime, particularly in projects involving sensitive or confidential information. 1.2 ISO 14001 – Environmental Management System ISO 14001 confirms that an organization actively manages its environmental impact. In IT services, this includes responsible resource usage, sustainable infrastructure practices and compliance with environmental regulations. For enterprise and public-sector clients, this certification signals that sustainability is embedded into operational decision-making, not treated as a marketing afterthought. 1.3 MSWiA Concession – Authorization for Security-Sensitive Software Projects The MSWiA (Polish Ministry of Interior and Administration) concession is a Polish government authorization required for companies delivering software solutions for police, military and other security-related institutions. It defines strict operational, organizational and personnel standards. In practice, this authorization covers work involving classified information, restricted-access systems and elements of critical national infrastructure. Possession of this concession proves that an IT partner is trusted to operate in environments where confidentiality, national security and procedural discipline are critical. 1.4 ISO 9001 – Quality Management System ISO 9001 governs how an organization ensures consistent quality in the way work is planned, executed and improved. Unlike security or service standards, it focuses on process discipline, repeatability and accountability across the entire delivery lifecycle. In software development, this translates into predictable project execution, clearly defined responsibilities, transparent communication and measurable outcomes. An ISO 9001-certified IT partner demonstrates that quality is not dependent on individual teams or people, but is embedded systemically across projects and client engagements. 1.5 ISO/IEC 20000 – IT Service Management System ISO/IEC 20000 addresses how IT services are operated and supported once they are in production. It defines best practices for service design, delivery, monitoring and continuous improvement, with a strong emphasis on availability, reliability and service continuity. This certification is particularly critical for managed services, long-term outsourcing and mission-critical systems, where operational stability matters as much as development capability. An ISO/IEC 20000-certified IT partner proves that IT services are managed as ongoing, business-critical operations rather than one-off technical deliverables. 1.6 ISO 45001 – Occupational Health and Safety Management System ISO 45001 defines how organizations protect employee health and safety. In IT, this includes workload management, operational resilience and creating stable working conditions for delivery teams. For clients, it indirectly translates into lower project risk, reduced staff turnover and higher continuity in complex, long-running initiatives. 1.7 ISO/IEC 42001 – Artificial Intelligence Management System 1.7.1 Setting a New Benchmark for Responsible AI ISO/IEC 42001 is the world’s first international standard dedicated exclusively to the management of artificial intelligence systems. It defines how organizations should design, develop, deploy and maintain AI in a trustworthy, transparent and accountable way. ISO/IEC 42001 directly supports key requirements of the EU AI Act, including structured AI risk management, defined human oversight mechanisms, lifecycle control and documentation of AI systems. TTMS is the first Polish company to receive certification under ISO/IEC 42001, confirmed through an audit conducted by TÜV Nord Poland. This places the company among the earliest operational adopters of this standard in Europe. The certification validates that TTMS’s Artificial Intelligence Management System (AIMS) meets international requirements for responsible AI governance, risk management and regulatory alignment. 1.7.2 Why ISO/IEC 42001 Matters Trust and credibility – AI systems are developed with formal governance, transparency and accountability. Risk-aware innovation – AI-related risks are identified, assessed and mitigated without slowing down delivery. Regulatory readiness – The framework supports alignment with evolving legal requirements, including the EU AI Act. Market leadership – Early adoption signals maturity and readiness for enterprise-scale AI projects. 1.7.3 What This Means for Clients and Partners Under ISO/IEC 42001, all AI components developed or integrated by TTMS are governed by a unified management system. This includes documentation, ethical oversight, lifecycle control and continuous monitoring. For organizations selecting an IT partner, this translates into lower compliance risk, stronger protection of users and data, and higher confidence that AI-enabled solutions are built responsibly from day one. 2. A Fully Integrated Management System Together, these seven certifications and authorizations operate within a comprehensive Integrated Management System (IMS). This means that security, quality, service delivery, sustainability, workforce safety and – increasingly critical – artificial intelligence governance are managed as interconnected processes rather than isolated compliance initiatives. For decision-makers comparing IT partners, this level of integration is not about checklists or logos. It significantly reduces organizational risk, increases operational consistency and enables vendors to deliver complex, regulated and future-proof digital solutions at scale, across long-term engagements. 3. Why Integrated Certification Matters for Clients In practice, this level of certification and integration delivers tangible benefits for clients: Reduced due diligence effort – certified processes shorten vendor assessment and compliance verification. Fewer client-side audits – independent third-party certification replaces repeated internal controls. Faster project onboarding – standardized governance accelerates contractual and operational startup. Lower compliance risk – regulatory, security and operational controls are embedded by default. Greater delivery predictability – projects run on proven, repeatable frameworks rather than ad hoc practices. In day-to-day cooperation, certified and integrated management systems simplify client onboarding, standardize reporting and reduce the scope and frequency of client-side audits. They also provide a stable foundation for clearly defined SLAs, escalation paths and compliance reporting, enabling faster project start-up and smoother long-term delivery. Ultimately, this level of certification significantly reduces the risks most often associated with selecting an IT partner. It limits dependency on individual people rather than processes, lowers the likelihood of unpredictable delivery models and minimizes the danger of vendor lock-in caused by undocumented or opaque practices. For decision-makers, certified and integrated management systems provide assurance that projects are governed by structure, transparency and continuity – not by improvisation. 4. From Certification to Execution Certifications matter only if they translate into real operational practices. At TTMS, quality, security and compliance frameworks are not treated as formal requirements, but as working management systems embedded into daily delivery. If your organization is evaluating an IT partner or looking to strengthen its own governance, quality management and compliance capabilities, TTMS supports clients across regulated industries in designing, implementing and operating certified management systems. Learn more about how we approach quality and integrated management in practice: Quality Management Services at TTMS FAQ Why are ISO certifications important when choosing an IT partner? ISO certifications provide independent verification that an IT partner operates according to internationally recognized standards. They reduce operational, security and compliance risks while increasing predictability and trust in long-term cooperation. Is ISO/IEC 27001 enough to ensure data security in IT projects? ISO/IEC 27001 is a strong foundation, but it works best as part of a broader management system. When combined with service management, quality and AI governance standards, it ensures security is embedded across the entire delivery lifecycle. What makes ISO/IEC 42001 different from other ISO standards? ISO/IEC 42001 is the first standard focused solely on artificial intelligence. It addresses AI-specific risks such as bias, transparency, accountability and regulatory compliance, which are not fully covered by traditional management systems. Why should enterprises care about AI management standards now? As AI becomes embedded in business-critical systems, regulatory scrutiny and ethical expectations are increasing. AI management standards help organizations avoid legal exposure while building sustainable, trustworthy AI solutions. How do multiple certifications benefit clients in real projects? Multiple certifications ensure that security, quality, service reliability, compliance and responsible innovation are managed consistently. For clients, this means fewer surprises, lower risk and higher confidence throughout the project lifecycle.
ReadTTMS at World Defense Show 2026 in Riyadh
Transition Technologies MS participated in World Defense Show 2026, held on 8-12 February in Riyadh, Saudi Arabia – one of the most significant global events dedicated to the defense and security sector. The exhibition confirmed a clear direction of technological development across the industry. Modern defense is increasingly shaped not only by hardware platforms, but by software, advanced analytics and artificial intelligence embedded directly into operational systems. Among the dominant themes observed during the event were: the growing deployment of hybrid VTOL unmanned aerial systems combining operational flexibility with extended range, the rapid expansion of virtual and simulation-based training environments using VR and AR technologies, deeper integration of AI into command support, fire control and situational awareness systems, and the continued evolution of integrated C2 and C4ISR architectures, particularly in the context of counter-UAS and air defense capabilities. A strong emphasis was also placed on autonomy and cost-effective air defense solutions, reflecting the operational challenges posed by the large-scale use of unmanned platforms in contemporary conflicts. For TTMS, World Defense Show 2026 provided an opportunity to engage in discussions on AI-driven decision support systems, advanced training platforms, and software layers supporting integrated defense architectures. The event enabled valuable exchanges with international partners and opened new perspectives for cooperation in complex, mission-critical environments. Participation in WDS 2026 reinforced the view that the future battlefield will be increasingly digital, interconnected and software-defined – and that effective defense transformation requires not only advanced platforms, but intelligent systems integrating data, sensors and operational decision-making.
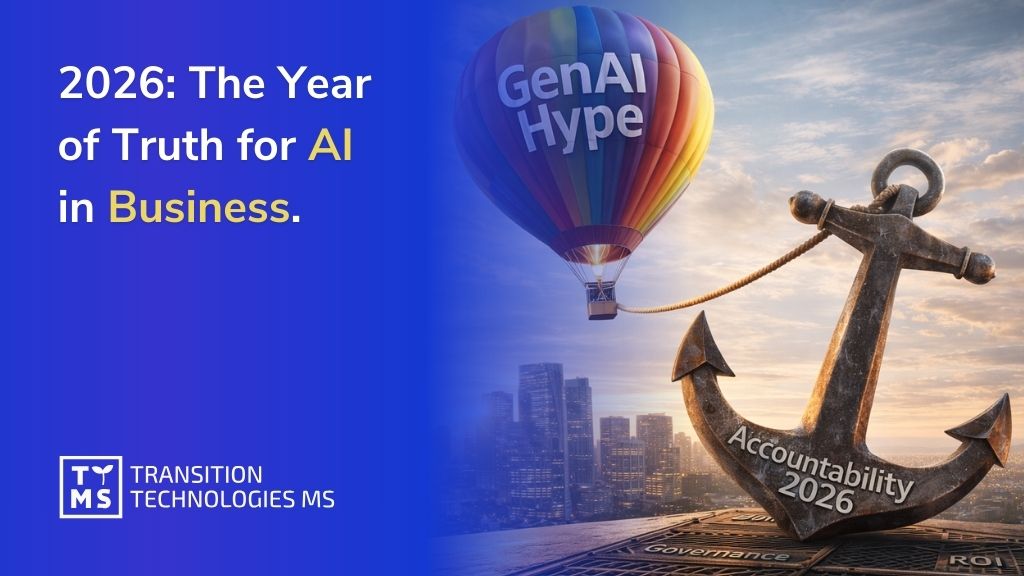
Read2026: The Year of Truth for AI in Business – Who Will Pay for the Experiments of 2023–2025?
1. Introduction: From Hype to Hard Truths For the past three years, artificial intelligence adoption in business has been driven by whirlwind hype and experimentation. Companies poured billions into generative AI pilots, eager to transform “literally everything” with AI. 2025, in particular, was the peak of this AI gold rush, as many firms moved from experiments to real deployments. Yet the reality lagged behind the promises – AI’s true impact remained uneven and hard to quantify, often because the surrounding systems and processes weren’t ready to support lasting results. As the World Economic Forum aptly noted, “If 2025 has been the year of AI hype, 2026 might be the year of AI reckoning”. In 2026, the bill for those early AI experiments is coming due in the form of technical debt, security risks, regulatory scrutiny, and investor impatience. 2026 represents a pivotal shift: the era of unchecked AI evangelism is giving way to an era of AI evaluation and accountability. The question businesses must answer now isn’t “Can AI do this?” but rather “How well can it do it, at what cost, and who bears the risk?”. This article examines how the freewheeling AI experiments of 2023-2025 created hidden costs and risks, and why 2026 is shaping up to be the year of truth for AI in business – a year when hype meets reality, and someone has to pay the price. 2. 2023-2025: A Hype-Driven AI Experimentation Era In hindsight, the years 2023 through 2025 were an AI wild west for many organizations. Generative AI (GenAI) tools like ChatGPT, Copilots, and custom models burst onto the scene, promising to revolutionize coding, content creation, customer service, and more. Tech giants and startups alike invested unprecedented sums in AI development and infrastructure, fueling a frenzy of innovation. Across nearly every industry, AI was touted as a transformative force, and companies raced to pilot new AI use cases to avoid being left behind. However, this rush came with a stark contradiction. Massive models and big budgets grabbed headlines, but the “lived reality” for businesses often fell short of the lofty promises. By late 2025, many organizations struggled to point to concrete improvements from their AI initiatives. The problem wasn’t that AI technology failed – in many cases, the algorithms worked as intended. Rather, the surrounding business processes and support systems were not prepared to turn AI outputs into durable value. Companies lacked the data infrastructure, change management, and integration needed to realize AI’s benefits at scale, so early pilots rarely matured into sustained ROI. Enthusiasm for AI nonetheless remained sky-high. Early missteps and patchy results did little to dampen the “AI race” mentality. If anything, failures shifted the conversation toward making AI work better. As one analysis put it, “Those moments of failure did not diminish enthusiasm – they matured initial excitement into a stronger desire for [results]”. By 2025, AI had moved decisively from sandbox to real-world deployment, and executives entered 2026 still convinced that AI is an imperative – but now wiser about the challenges ahead. 3. The Mounting Technical & Security Debt from Rapid AI Adoption One of the hidden costs of the 2023-2025 AI rush is the significant technical debt and security debt that many organizations accumulated. In the scramble to deploy AI solutions quickly, shortcuts were taken – especially in areas like AI-generated code and automated workflows – that introduced long-term maintenance burdens and vulnerabilities. AI coding assistants dramatically accelerated software development, enabling developers to churn out code up to 2× faster. But this velocity came at a price. Studies found that AI-generated code often favors quick fixes over sound architecture, leading to bugs, security vulnerabilities, duplicated code, and unmanageable complexity piling up in codebases. As one report noted, “the immense velocity gain inherently increases the accumulation of code quality liabilities, specifically bugs, security vulnerabilities, structural complexity, and technical debt”. Even as AI coding tools improve, the sheer volume of output overwhelms human code review processes, meaning bad code slips through. The result: a growing backlog of “structurally weak” code and latent defects that organizations must now pay to refactor and secure. Forrester researchers predict that by 2026, 75% of technology decision-makers will be grappling with moderate to severe technical debt, much of it due to the speed-first, AI-assisted development approach of the preceding years. This technical debt isn’t just a developer headache – it’s an enterprise risk. Systems riddled with AI-introduced bugs or poorly maintained AI models can fail in unpredictable ways, impacting business operations and customer experiences. Security leaders are likewise sounding alarms about “security debt” from rapid GenAI adoption. In the rush to automate tasks and generate code/content with AI, many companies failed to implement proper security guardrails. Common issues include: Unvetted AI-generated code with hidden vulnerabilities (e.g. insecure APIs or logic flaws) being deployed into production systems. Attackers can exploit these weaknesses if not caught. “Shadow AI” usage by employees – workers using personal ChatGPT or other AI accounts to process company data – leading to sensitive data leaks. For example, in 2023, Samsung engineers accidentally leaked confidential source code to ChatGPT, prompting the company to ban internal use of generative AI until controls were in place. Samsung’s internal survey found 65% of participants saw GenAI tools as a security risk, citing the inability to retrieve data once it’s on external AI servers. Many firms have since discovered employees pasting client data or source code into AI tools without authorization, creating compliance and IP exposure issues. New attack vectors via AI integrations. As companies wove AI into products and workflows, they sometimes created fresh vulnerabilities. Threat actors are now leveraging generative AI to craft more sophisticated cyberattacks at machine speed, from convincing phishing emails to code exploits. Meanwhile, AI services integrated into apps could be manipulated (via prompt injection or data poisoning) unless properly secured. The net effect is that security teams enter 2026 with a backlog of AI-related risks to mitigate. Regulators, customers, and auditors are increasingly expecting “provable security controls across the AI lifecycle (data sourcing, training, deployment, monitoring, and incident response)”. In other words, companies must now pay down the security debt from their rapid AI uptake by implementing stricter access controls, data protection measures, and AI model security testing. Even cyber insurance carriers are reacting – some insurers now require evidence of AI risk management (like adversarial red-teaming of AI models and bias testing) before providing coverage. Bottom line: The experimentation era accelerated productivity but also spawned hidden costs. In 2026, businesses will have to invest time and money to clean up “AI slop” – refactoring shaky AI-generated code, patching vulnerabilities, and instituting controls to prevent data leaks and abuse. Those that don’t tackle this technical and security debt will pay in other ways, whether through breaches, outages, or stymied innovation. 4. The Governance Gap: AI Oversight Didn’t Keep Up Another major lesson from the 2023-2025 AI boom is that AI adoption raced ahead of governance. In the frenzy to deploy AI solutions, many organizations neglected to establish proper AI governance, audit trails, and internal controls. Now, in 2026, that oversight gap is becoming painfully clear. During the hype phase, exciting AI tools were often rolled out with minimal policy guidance or risk assessment. Few companies had frameworks in place to answer critical questions like: Who is responsible for AI decision outcomes? How do we audit what the AI did? Are we preventing bias, IP misuse, or compliance violations by our AI systems? The result is that many firms operated on AI “trust” without “verify.” For instance, employees were given AI copilots to generate code or content, but organizations lacked audit logs or documentation of what the AI produced and whether humans reviewed it. Decision-making algorithms were deployed without clear accountability or human-in-the-loop checkpoints. In a PwC survey, nearly half of executives admitted that putting Responsible AI principles into practice has been a challenge. While a strong majority agree that “responsible AI” is crucial for ROI and efficiency, operationalizing those principles (through bias testing, transparency, control mechanisms) lagged behind. In fact, AI adoption has spread faster than the governance models to manage its unique risks. Companies eagerly implemented AI agents and automated decision systems, “spreading faster than governance models can address their unique needs”. This governance gap means many organizations entered 2026 with AI systems running in production that have no rigorous oversight or documentation, creating risk of errors or ethical lapses. The early rush to AI often prioritized speed over strategy, as one tech legal officer observed. “The early rush to adopt AI prioritized speed over strategy, leaving many organizations with little to show for their investments,” says Ivanti’s Chief Legal Officer, noting that companies are now waking up to the consequences of this lapse. Those consequences include fragmented, siloed AI projects, inconsistent standards, and “innovation theater” – lots of AI pilot activity with no cohesive strategy or measurable value to the business. Crucially, lack of governance has become a board-level issue by 2026. Corporate directors and investors are asking management: What controls do you have over your AI? Regulators, too, expect to see formal AI risk management and oversight structures. In the U.S., the SEC’s Investor Advisory Committee has even called for enhanced disclosures on how boards oversee AI governance as part of managing cybersecurity risks. This means companies could soon have to report how they govern AI use, similar to how they disclose financial controls or data security practices. The governance gap of the last few years has left many firms playing catch-up. Audit and compliance teams in 2026 are now scrambling to inventory all AI systems in use, set up AI audit trails, and enforce policies (e.g. requiring human review of AI outputs in high-stakes decisions). Responsible AI frameworks that were mostly talk in 2023-24 are (hopefully) becoming operational in 2026. As PwC predicts, “2026 could be the year when companies overcome this challenge and roll out repeatable, rigorous RAI (Responsible AI) practices”. We are likely to see new governance mechanisms take hold: from AI model registers and documentation requirements, to internal AI ethics committees, to tools for automated bias detection and monitoring. The companies that close this governance gap will not only avoid costly missteps but also be better positioned to scale AI in a safe, trusted manner going forward. 5. Speed vs. Readiness: The Deployment-Readiness Gap Widens One striking issue in the AI boom was the widening gap between how fast companies deployed AI and how prepared their organizations were to manage its consequences. Many businesses leapt from zero to AI at breakneck speed, but their people, processes, and strategies lagged behind, creating a performance paradox: AI was everywhere, yet tangible business value was often elusive. By the end of 2025, surveys revealed a sobering statistic – up to 95% of enterprise generative AI projects had failed to deliver measurable ROI or P&L impact. In other words, only a small fraction of AI initiatives actually moved the needle for the business. The MIT Media Lab found that “95% of organizations see no measurable returns” from AI in the knowledge sector. This doesn’t mean AI can’t create value; rather, it underscores that most companies weren’t ready to capture value at the pace they deployed AI. The reasons for this deployment-readiness gap are multi-fold: Lack of integration with workflows: Deploying an AI model is one thing; redesigning business processes to exploit that model is another. Many firms “introduced AI without aligning it to legacy processes or training staff,” leading to an initial productivity dip known as the AI productivity paradox. AI outputs appeared impressive in demos, but front-line employees often couldn’t easily incorporate them into daily work, or had to spend extra effort verifying AI results (what some call “AI slop” or low-quality output that creates more work). Skills and culture lag: Companies deployed AI faster than they upskilled their workforce to use and oversee these tools. Employees were either fearful of the new tech or not trained to collaborate with AI systems effectively. As Gartner analyst Deepak Seth noted, “we still don’t understand how to build the team structure where AI is an equal member of the team”. Many organizations lacked AI fluency among staff and managers, resulting in misuse or underutilization of the technology. Scattered, unprioritized efforts: Without a clear AI strategy, some companies spread themselves thin over dozens of AI experiments. “Organizations spread their efforts thin, placing small sporadic bets… early wins can mask deeper challenges,” PwC observes. With AI projects popping up everywhere (often bottom-up from enthusiastic employees), leadership struggled to scale the ones that mattered. The absence of a top-down strategy meant many AI projects never translated into enterprise-wide impact. The result of these factors was that by 2025, many businesses had little to show for their flurry of AI activity. As Ivanti’s Brooke Johnson put it, companies found themselves with “underperforming tools, fragmented systems, and wasted budgets” because they moved so fast without a plan. This frustration is now forcing a change in 2026: a shift from “move fast and break things” to “slow down and get it right.” Already, we see leading firms adjusting their approach. Rather than chasing dozens of AI use cases, they are identifying a few high-impact areas and focusing deeply (the “go narrow and deep” approach). They are investing in change management and training so that employees actually adopt the AI tools provided. Importantly, executives are injecting more discipline and oversight into AI initiatives. “There is – rightfully – little patience for ‘exploratory’ AI investments” in 2026, notes PwC; every dollar now needs to “fuel measurable outcomes”, and frivolous pilots are being pruned. In other words, AI has to earn its keep now. The gap between deployment and readiness is closing at companies that treat AI as a strategic transformation (led by senior leadership) rather than a series of tech demos. Those still stuck in “innovation theater” will find 2026 a harsh wake-up call – their AI projects will face scrutiny from CFOs and boards asking “What value is this delivering?” Success in 2026 will favor the organizations that balance innovation with preparation, aligning AI projects to business goals, fortifying them with the right processes and talent, and phasing deployments at a pace the organization can absorb. The days of deploying AI for AI’s sake are over; now it’s about sustainable, managed AI that the organization is ready to leverage. 6. Regulatory Reckoning: AI Rules and Enforcement Arrive Regulators have taken notice of the AI free-for-all of recent years, and 2026 marks the start of a more forceful regulatory response worldwide. After a period of policy debate in 2023-2024, governments are now moving from guidelines to enforcement of AI rules. Businesses that ignored AI governance may find themselves facing legal and financial consequences if they don’t adapt quickly. In the European Union, a landmark law – the EU AI Act – is coming into effect in phases. Adopted in late 2023, this comprehensive regulation imposes requirements based on AI risk levels. Notably, by August 2, 2026, companies deploying AI in the EU must comply with specific transparency rules and controls for “high-risk AI systems.” Non-compliance isn’t an option unless you fancy huge fines – penalties can go up to €35 million or 7% of global annual turnover (whichever is higher) for serious violations. This is a clear signal that the era of voluntary self-regulation is over in the EU. Companies will need to document their AI systems, conduct risk assessments, and ensure human oversight for high-risk applications (e.g. AI in healthcare, finance, HR, etc.), or face hefty enforcement. EU regulators have already begun flexing their muscles. The first set of AI Act provisions kicked in during 2025, and regulators in member states are being appointed to oversee compliance. The European Commission is issuing guidance on how to apply these rules in practice. We also see related moves like Italy’s AI law (aligned with the EU Act) and a new Code of Practice on AI-generated content transparency being rolled out. All of this means that by 2026, companies operating in Europe need to have their AI house in order – keeping audit trails, registering certain AI systems in an EU database, providing user disclosures for AI-generated content, and more – or risk investigations and fines. North America is not far behind. While the U.S. hasn’t passed a sweeping federal AI law as of early 2026, state-level regulations and enforcements are picking up speed. For example, Colorado’s AI Act (enacted 2024) takes effect in June 2026, imposing requirements on AI developers and users to avoid algorithmic discrimination, implement risk management programs, and conduct impact assessments for AI involved in important decisions. Several other states (California, New York, Illinois, etc.) have introduced AI laws targeting specific concerns like hiring algorithms or AI outputs that impersonate humans. This patchwork of state rules means companies in the U.S. must navigate compliance carefully or face state attorney general actions. Indeed, 2025 already saw the first signs of AI enforcement in the U.S.: In May 2025, the Pennsylvania Attorney General reached a settlement with a property management company after its use of an AI rental decision tool led to unsafe housing conditions and legal violations. In July 2025, the Massachusetts AG fined a student loan company $2.5 million over allegations that its AI-powered system unfairly delayed or mismanaged student loan relief. These cases are likely the tip of the iceberg – regulators are signaling that companies will be held accountable for harmful outcomes of AI, even using existing consumer protection or anti-discrimination laws. The U.S. Federal Trade Commission has also warned it will crack down on deceptive AI practices and data misuse, launching inquiries into chatbot harms and children’s safety in AI apps. Across the Atlantic, the UK is shifting from principles to binding rules as well. After initially favoring a light-touch, pro-innovation stance, the UK government indicated in 2025 that sector regulators will be given explicit powers to enforce AI requirements in areas like data protection, competition, and safety. By 2026, we can expect the UK to introduce more concrete compliance obligations (though likely less prescriptive than the EU’s approach). For business leaders, the message is clear: the regulatory landscape for AI is rapidly solidifying in 2026. Companies need to treat AI compliance with the same seriousness as data privacy (GDPR) or financial reporting. This includes: conducting AI impact assessments, ensuring transparency (e.g. informing users when AI is used), maintaining documentation and audit logs of AI system decisions, and implementing processes to handle AI-related incidents or errors. Those who fail to do so may find regulators making an example of them – and the fines or legal damages will effectively “make them pay” for the lax practices of the past few years. 7. Investor Backlash: Demanding ROI and Accountability It’s not just regulators – investors and shareholders have also lost patience with AI hype. By 2026, the stock market and venture capitalists alike are looking for tangible returns on AI investments, and they are starting to punish companies that over-promised and under-delivered on AI. In 2025, AI was the belle of the ball on Wall Street – AI-heavy tech stocks soared, and nearly every earnings call featured some AI angle. But as 2026 kicks off, analysts are openly asking AI players to “show us the money.” A report summarized the mood with a dating analogy: “In 2025, AI took investors on a really nice first date. In 2026… it’s time to start footing the bill.”. The grace period for speculative AI spending is ending, and investors expect to see clear ROI or cost savings attributable to AI initiatives. Companies that can’t quantify value may see their valuations marked down. We are already seeing the market sorting AI winners from losers. Tom Essaye of Sevens Report noted in late 2025 that the once “unified enthusiasm” for all things AI had become “fractured”, with investors getting choosier. “The industry is moving into a period where the market is aggressively sorting winners and losers,” he observed. For example, certain chipmakers and cloud providers that directly benefit from AI workloads boomed, while some former software darlings that merely marketed themselves as AI leaders have seen their stocks stumble as investors demand evidence of real AI-driven growth. Even big enterprise software firms like Oracle, which rode the AI buzz, faced more scrutiny as investors asked for immediate ROI from AI efforts. This is a stark change from 2023, when a mere mention of “AI strategy” could boost a company’s stock price. Now, companies must back up the AI story with numbers – whether it’s increased revenue, improved margins, or new customers attributable to AI. Shareholders are also pushing companies on the cost side of AI. Training large AI models and running them at scale is extremely expensive (think skyrocketing cloud bills and GPU purchases). In 2026’s tighter economic climate, boards and investors won’t tolerate open-ended AI spending without a clear business case. We may see some investor activism or tough questioning in annual meetings: e.g., “You spent $100M on AI last year – what did we get for it?” If the answer is ambiguous, expect backlash. Conversely, firms that can articulate and deliver a solid AI payoff will be rewarded with investor confidence. Another aspect of investor scrutiny is corporate governance around AI (as touched on earlier). Sophisticated investors worry that companies without proper AI governance may face reputational or legal disasters (which hurt shareholder value). This is why the SEC and investors are calling for board-level oversight of AI. It won’t be surprising if in 2026 some institutional investors start asking companies to conduct third-party audits of their AI systems or to publish AI risk reports, similar to sustainability or ESG reports. Investor sentiment is basically saying: we believe AI can be transformative, but we’ve been through hype cycles before – we want to see prudent management and real returns, not just techno-optimism. In summary, 2026 is the year AI hype meets financial reality. Companies will either begin to reap returns on their AI investments or face tough consequences. Those that treated the past few years as an expensive learning experience must now either capitalize on that learning or potentially write off failed projects. For some, this reckoning could mean stock price corrections or difficulty raising funds if they can’t demonstrate a path to profitability with AI. For others who have sound AI strategies, 2026 could be the year AI finally boosts the bottom line and vindicates their investments. As one LinkedIn commentator quipped, “2026 won’t be defined by hype. It will be defined by accountability – especially by cost and return on investment.” 8. Case Studies: AI Maturity Winners and Losers Real-world examples illustrate how companies are faring as the experimental AI tide goes out. Some organizations are emerging as AI maturity winners – they invested in governance and alignment early, and are now seeing tangible benefits. Others are struggling or learning hard lessons, having to backtrack on rushed AI deployments that didn’t pan out. On the struggling side, a cautionary tale comes from those who sprinted into AI without guardrails. The Samsung incident mentioned earlier is a prime example. Eager to boost developer productivity, Samsung’s semiconductor division allowed engineers to use ChatGPT – and within weeks, internal source code and sensitive business plans were inadvertently leaked to the public chatbot. The fallout was swift: Samsung imposed an immediate ban on external AI tools until it could implement proper data security measures. This underscores that even tech-savvy companies can trip up without internal AI policies. Many other firms in 2023-24 faced similar scares (banks like JPMorgan temporarily banned ChatGPT use, for instance), realizing only after a leak or an embarrassing output that they needed to enforce AI usage guidelines and logging. The cost here is mostly reputational and operational – these companies had to pause promising AI applications until they cleaned up procedures, costing them time and momentum. Another “loser” scenario is the media and content companies that embraced AI too quickly. In early 2023, several digital publishers (BuzzFeed, CNET, etc.) experimented with AI-written articles to cut costs. It backfired when readers and experts found factual errors and plagiarism in the AI content, leading to public backlash and corrections. CNET, for example, quietly had to halt its AI content program after significant mistakes were exposed, undermining trust. These cases highlight that rushing AI into customer-facing outputs without rigorous review can damage a brand and erode customer trust – a hard lesson learned. On the flip side, some companies have navigated the AI boom adeptly and are now reaping rewards: Ernst & Young (EY), the global consulting and tax firm, is a showcase of AI at scale with governance. EY early on created an “AI Center of Excellence” and established policies for responsible AI use. The result? By 2025, EY had 30 million AI-enabled processes documented internally and 41,000 AI “agents” in production supporting their workflows. One notable agent, EY’s AI-driven tax advisor, provides up-to-date tax law information to employees and clients – an invaluable tool in a field with 100+ regulatory changes per day. Because EY paired AI deployment with training (upskilling thousands of staff) and controls (every AI recommendation in tax gets human sign-off), they have seen efficiency gains without losing quality. EY’s leadership claims these AI tools have significantly boosted productivity in back-office processing and knowledge management, giving them a competitive edge. This success wasn’t accidental; it came from treating AI as a strategic priority and investing in enterprise-wide readiness. DXC Technology, an IT services company, offers another success story through a human-centric AI approach. DXC integrated AI as a “co-pilot” for its cybersecurity analysts. They deployed an AI agent as a junior analyst in their Security Operations Center to handle routine tier-1 tasks (like classifying incoming alerts and documenting findings). The outcome has been impressive: DXC cut investigation times by 67.5% and freed up 224,000 analyst hours in a year. Human analysts now spend those hours on higher-value work such as complex threat hunting, while mundane tasks are efficiently automated. DXC credits this to designing AI to complement (not replace) humans, and giving employees oversight responsibilities to “spot and correct the AI’s mistakes”. Their AI agent operates within a well-monitored workflow, with clear protocols for when to escalate to a human. The success of DXC and EY underscores that when AI is implemented with clear purpose, guardrails, and employee buy-in, it can deliver substantial ROI and risk reduction. In the financial sector, Morgan Stanley gained recognition for its careful yet bold AI integration. The firm partnered with OpenAI to create an internal GPT-4-powered assistant that helps financial advisors sift through research and internal knowledge bases. Rather than rushing it out, Morgan Stanley spent months fine-tuning the model on proprietary data and setting up compliance checks. The result was a tool so effective that within months of launch, 98% of Morgan’s advisor teams were actively using it daily, dramatically improving their productivity in answering client queries. Early reports suggested the firm anticipated over $1 billion in ROI from AI in the first year. Morgan Stanley’s stock even got a boost amid industry buzz that they had cracked the code on enterprise AI value. Their approach – start with a targeted use case (research Q&A), ensure data is clean and permissions are handled, and measure impact – is becoming a template for successful AI rollout in other banks. These examples illustrate a broader point: the “winners” in 2026 are those treating AI as a long-term capability to be built and managed, not a quick fix or gimmick. They invested in governance, employee training, and aligning AI to business strategy. The “losers” rushed in for short-term gains or buzz, only to encounter pitfalls – be it embarrassed executives having to roll back a flawed AI system, or angry customers and regulators on the doorstep. As 2026 unfolds, we’ll likely see more of this divergence. Some companies will quietly scale back AI projects that aren’t delivering (essentially writing off the sunk costs of 2023-25 experiments). Others will double-down but with a new seriousness: instituting AI steering committees, hiring Chief AI Officers or similar roles to ensure proper oversight, and demanding that every AI project has clear metrics for success. This period will separate the leaders from the laggards in AI maturity. And as the title suggests, those who led with hype will “pay” – either in cleanup costs or missed opportunities – while those who paired innovation with responsibility will thrive. 9. Conclusion: 2026 and Beyond – Accountability, Maturity, and Sustainable AI The year 2026 heralds a new chapter for AI in business – one where accountability and realism trump hype and experimentation. The free ride is over: companies can no longer throw AI at problems without owning the outcomes. The experiments of 2023-2025 are yielding a trove of lessons, and the bill for mistakes and oversights is coming due. Who will pay for those past experiments? In many cases, businesses themselves will pay, by investing heavily now to bolster security, retrofit governance, and refine AI models that were rushed out. Some will pay in more painful ways – through regulatory fines, legal liabilities, or loss of market share to more disciplined competitors. Senior leaders who championed flashy AI initiatives will be held to account for their ROI. Boards will ask tougher questions. Regulators will demand evidence of risk controls. Investors will fund only those AI efforts that demonstrate clear value or at least a credible path to it. Yet, 2026 is not just about reckoning – it’s also about the maturation of AI. This is the year where AI can prove its worth under real-world constraints. With hype dissipating, truly valuable AI innovations will stand out. Companies that invested wisely in AI (and managed its risks) may start to enjoy compounding benefits, from streamlined operations to new revenue streams. We might look back on 2026 as the year AI moved from the “peak of inflated expectations” to the “plateau of productivity,” to borrow Gartner’s hype cycle terms. For general business leaders, the mandate going forward is clear: approach AI with eyes wide open. Embrace the technology – by all indications it will be as transformative as promised in the long run – but do so with a framework for accountability. This means instituting proper AI governance, investing in employee skills and change management, monitoring outcomes diligently, and aligning every AI project with strategic business goals (and constraints). It also means being ready to hit pause or pull the plug on AI deployments that pose undue risk or fail to deliver value, no matter how shiny the technology. The reckoning of 2026 is ultimately healthy. It marks the transition from the “move fast and break things” era of AI to a “move smart and build things that last” era. Companies that internalize this shift will not only avoid the costly pitfalls of the past, they will also position themselves to harness AI’s true power sustainably – turning it into a trusted engine of innovation and efficiency within well-defined guardrails. Those that don’t adjust may find themselves paying the price in more ways than one. As we move beyond 2026, one hopes that the lessons of the early 2020s will translate into a new balance: where AI’s incredible potential is pursued with both boldness and responsibility. The year of truth will have served its purpose if it leaves the business world with clearer-eyed optimism – excited about what AI can do, yet keenly aware of what it takes to do it right. 10. From AI Reckoning to Responsible AI Execution For organizations entering this new phase of AI accountability, the challenge is no longer whether to use AI, but how to operationalize it responsibly, securely, and at scale. Turning AI from an experiment into a sustainable business capability requires more than tools – it demands governance, integration, and real-world execution experience. This is where TTMS supports business leaders. Through its AI solutions for business, TTMS helps organizations move beyond pilot projects and hype-driven deployments toward production-ready, enterprise-grade AI systems. The focus is on aligning AI with business processes, mitigating technical and security debt, embedding governance and compliance by design, and ensuring that AI investments deliver measurable outcomes. In a year defined by accountability, execution quality is what separates AI leaders from AI casualties. 👉 https://ttms.com/ai-solutions-for-business/ FAQ: AI’s 2026 Reckoning – Key Questions Answered Why is 2026 called the “year of truth” for AI in business? Because many organizations are moving from experimentation to accountability. In 2023-2025, it was easy to launch pilots, buy licenses, and announce “AI initiatives” without proving impact or managing the risks properly. In 2026, boards, investors, customers, and regulators increasingly expect evidence: measurable outcomes, clear ownership, and documented controls. This shift turns AI from a trendy capability into an operational discipline. If AI is embedded in key processes, leaders must answer for errors, bias, security incidents, and financial performance. In practice, “year of truth” means companies will be judged not on how much AI they use, but on how well they govern it and whether it reliably improves business results. What does it mean when people say AI is no longer a competitive advantage? It means access to AI has become widely available, so simply “using AI” doesn’t set a company apart anymore. The differentiator is now execution: how well AI is integrated into real workflows, how consistently it delivers quality, and how safely it operates at scale. Two companies can deploy the same tools, but get very different outcomes depending on their data readiness, process design, and organizational maturity. Leaders who treat AI like infrastructure – with standards, monitoring, and continuous improvement – usually outperform those who treat it like a series of isolated pilots. Competitive advantage shifts from the model itself to the surrounding system: governance, change management, and the ability to turn AI outputs into decisions and actions that create value. How can rapid GenAI adoption increase security risk instead of reducing it? GenAI can accelerate delivery, but it can also accelerate mistakes. When teams generate code faster, they may ship more changes, more often, and with less time for reviews or threat modeling. This can increase misconfigurations, insecure patterns, and hidden vulnerabilities that only show up later, when attackers exploit them. GenAI also creates new exposure routes when employees paste sensitive data into external tools, or when AI features are connected to business systems without strong access controls. Over time, these issues accumulate into “security debt” – a growing backlog of risk that becomes expensive to fix under pressure. The core problem isn’t that GenAI is “unsafe by nature”, but that organizations often adopt it faster than they build the controls needed to keep it safe. hat should business leaders measure to know whether AI is really working? Leaders should measure outcomes, not activity. Useful metrics depend on the use case, but typically include time-to-completion, error rate, cost per transaction, customer satisfaction, and cycle time from idea to delivery. For AI in software engineering, look at deployment frequency together with stability indicators like incident rate, rollback frequency, and time-to-repair, because speed without reliability is not success. For AI in customer operations, measure resolution rates, escalations to humans, compliance breaches, and rework. It’s also critical to measure adoption and trust: how often employees use the tool, how often they override it, and why. Finally, treat governance as measurable too: do you have audit trails, role-based access, documented model changes, and a clear owner accountable for outcomes? What does “AI governance” look like in practice for a global organization? AI governance is the set of rules, roles, and controls that make AI predictable, safe, and auditable. In practice, it starts with a clear inventory of where AI is used, what data it touches, and what decisions it influences. It includes policies for acceptable use, risk classification of AI systems, and defined approval steps for high-impact deployments. It also requires ongoing monitoring: quality checks, bias testing where relevant, security testing, and incident response plans when AI outputs cause harm. Governance is not a one-time document – it’s an operating model with accountability, documentation, and continuous improvement. For global firms, governance also means aligning practices across regions and functions while respecting local regulations and business realities, so that AI can scale without chaos.
ReadData security in a remote collaboration model – access and abuse risks
IT outsourcing to countries outside the European Union and the United States has long ceased to be something exotic. For many companies, it has become a normal element of day-to-day IT operations. Access to large teams of specialists, the ability to scale quickly, and lower costs have led to centers located in Asia, especially India, taking over a significant part of technology projects delivered for organizations in Europe and North America. Today, these are no longer only auxiliary tasks. Offshore teams are increasingly responsible for maintaining critical systems, working with sensitive data, and handling processes that have a direct impact on business continuity. The greater the scale of such cooperation, the greater the responsibility transferred to external teams. This, in turn, means growing exposure to information security risks. In practice, many of these threats are not visible at the stage of selecting a provider or negotiating the contract. They only become apparent during day-to-day operations, when formal arrangements start to function in the reality of remote work, staff turnover, and limited control over the environment in which data is processed. Importantly, modern security incidents in IT outsourcing are increasingly less often the result of obvious technological shortcomings. Much more frequently, their source lies in the way work is organized. Broadly granted permissions, simplified access procedures, and processes vulnerable to internal abuse create an environment in which legitimate access becomes the main risk vector. In such a model, the threat shifts from technology to people, operational decisions, and the way access to systems and data is managed. 1. Why the international IT service model changes the cyber risk profile India has for years been one of the main reference points for global IT outsourcing. This is primarily due to the scale of the available teams and the level of technical competence, which makes it possible to handle large volumes of similar tasks in an orderly and predictable way. For many international organizations, this means the ability to deliver projects quickly and provide stable operational support without having to expand their own structures. That same scale which provides efficiency also affects how work and access rights are organized. In distributed teams, permissions to systems are often granted broadly and for longer periods so as not to block continuity of operations. User roles are standardized, and access is granted to entire groups, which simplifies team management but at the same time limits precise control over who uses which resources and to what extent. The repeatability of processes additionally means that the way work is performed becomes easy to predict, and some decisions are made automatically. On top of this model comes pressure to meet performance indicators. Response time, number of handled tickets, or system availability become priorities, which in practice leads to simplifying procedures and bypassing part of the control mechanisms. From a security perspective, this means increased risk of access abuse and activities that go beyond real operational needs. Under such conditions, incidents rarely take the form of classic external attacks. Much more often, they are the result of errors, lack of ongoing oversight, or deliberate actions undertaken within permissions that were formally granted in line with procedure. 2. Cyber threats in a distributed model – a broader business context In recent years, digital fraud, phishing, and other forms of abuse have become a global problem affecting organizations regardless of industry or location. More and more often, they are not the result of breaking technical safeguards but of exploiting operational knowledge, established patterns of action, and access to systems. In this context, international IT outsourcing should be analyzed without oversimplification and without shifting responsibility onto specific markets. The example of India clearly shows that what really matters is not the physical location of teams, but the common denominator of operational models based on large scale, work according to predefined scripts, and broad access to data. These are the very elements that create an environment in which process repeatability and operational pressure can lead to lower vigilance and the automation of decisions, including those related to security. In such conditions, the line between a simple operational error and a full-scale security incident becomes very thin. A single event that would have limited impact in another context can quickly escalate into systemic consequences. From a business perspective, this means the need to look at cyber threats in IT outsourcing in a broader way than just through the lens of technology and location, and much more through the way work is organized and access to data is managed. 3. Data access as the main risk vector In IT outsourcing, the biggest security issues increasingly seldom begin in the code or the application architecture itself. In practice, the starting point is much more often access to data and systems. This is especially true for environments in which many teams work in parallel on the same resources and the scope of granted permissions is broad and difficult to control on an ongoing basis. Under such conditions, it is access management – rather than code quality – that most strongly determines the level of real risk. The most sensitive areas are those where access to production systems is part of everyday work. This applies to technical support teams, both first and second line, which have direct contact with user data and live environments. A similar situation occurs in quality assurance teams, where tests are often run on data that is very close to production data. Additionally, there are back-office processes related to customer service, covering financial systems, contact data, and identification information. In these areas, a single compromised access can have consequences far beyond the original scope of permissions. It can open the way for further privilege escalation, data copying, or leveraging existing trust to carry out effective social engineering attacks against end users. Importantly, such incidents rarely require advanced technical techniques. They often rely on legitimately granted permissions, insufficient monitoring, and trust mechanisms embedded in everyday operational processes. 3.1 Why technical support (L1/L2) is particularly sensitive First- and second-line support teams often have broad access to systems – not because it is strictly necessary to perform their tasks, but because granting permissions “in advance” is operationally easier than managing contextual access. In practice, this means that a helpdesk employee may be able to view customer data, reset administrator passwords, or access infrastructure management tools. Additionally, high turnover in such teams means that offboarding processes are often delayed or incomplete. As a result, a situation may arise in which a former employee still has an active account with permissions to production systems – even though their cooperation with the provider has formally ended. 3.2 QA teams and production data – an underestimated risk Quality assurance teams often work on copies of production data or on test environments that contain real customer data. Although formally these are “test data”, in practice they may include full sets of personal information, transaction data, or sensitive business data. The problem is that test environments are rarely subject to the same rigorous oversight as production systems. They often lack mechanisms such as encryption at rest, detailed access logging, or user activity monitoring. This makes data in QA environments an easier target than data in production systems – while incidents often remain invisible from the client’s perspective. 3.3 Back-office processes – operational knowledge as a weapon Employees handling back-office administrative processes have not only technical access but also operational knowledge: they know procedures, communication patterns, organizational structures, and how systems work. This makes them potentially effective participants in social engineering attacks – both as victims and, in extreme cases, as conscious or unconscious accomplices in abuse. Combined with KPI pressure, work according to rigid scripts, and limited awareness of the broader security context, these processes become vulnerable to manipulation, data exfiltration, and incidents based on trust and routine. 4. Security certificates vs. real data protection Outsourcing providers very often meet formal security requirements and hold the relevant certificates. The problem is that certification does not control how permissions are used in everyday work. In distributed work environments, persistent challenges include high employee turnover, delays in revoking permissions, remote work, and limited monitoring of user activity. As a result, a gap arises between declared compliance and the actual level of data protection. 5. When IT outsourcing increases exposure to cyber threats Cooperation with an external partner in an IT outsourcing model can increase exposure to cyber threats, but only when the way it is organized does not take real security conditions into account. This applies, among other things, to situations where access to systems is granted permanently and is not subject to regular review. Over time, permissions begin to function independently of the actual scope of duties and are treated as part of the fixed working environment rather than as a conscious operational decision. A significant problem is also limited visibility into how data and systems are used on the provider’s side. If user activity monitoring, log analysis, and ongoing operational control are outside the direct oversight of the contracting organization, the ability to detect irregularities early is significantly reduced. Additionally, responsibility for information security is often blurred between the client and the provider, which makes it harder to respond clearly in ambiguous or disputed situations. Under such conditions, even a single incident can quickly spread to a broader part of the organization. The access of one user or one technical account may be enough as a starting point for privilege escalation and abuses affecting many systems at once. What’s worse, such events are often detected late – only when real operational, financial, or reputational damage has already occurred and the room for maneuver on the organization’s side is already heavily constrained. 6. How companies reduce digital security risk in IT outsourcing More and more companies are concluding that information security in a remote model cannot be effectively protected solely with classic technical safeguards. Distributed teams, work across multiple time zones, and access to systems from different locations all mean that an approach based only on network perimeter protection is no longer sufficient. As a result, organizations are shifting their attention to where risk most often emerges, namely to the way access to data and systems is managed. In practice, this means more deliberate restriction of permissions and splitting access into smaller, precisely defined scopes. Users receive only the rights that are necessary to perform specific tasks, rather than full access derived from their role or job title. At the same time, the importance of activity monitoring is growing, including observing unusual behavior, repeated deviations from standard working patterns, and attempts to reach resources that are not related to current responsibilities. An increasingly common approach is also a model based on the absence of implicit trust, known as zero trust. It assumes that every access request should be verified regardless of where the user is located, what role they perform, and from where they work. This is complemented by separating sensitive processes across different teams and regions so that a single access point does not allow full control over the entire process or a complete set of data. Ultimately, however, what matters most is whether these assumptions actually work in everyday operations. If they remain only written in documents or declared at the policy level, they do not translate into real risk reduction. Only consistent enforcement of rules, regular access reviews, and genuine visibility into user actions make it possible to reduce an organization’s vulnerability to security incidents. 7. Conclusions IT outsourcing itself is not a threat to an organization’s security. This applies to cooperation with teams in India as well as in other regions of the world. The problem begins when the scale of operations grows faster than awareness of risks related to cybersecurity. In environments where many teams have broad access to data and the pace of work is driven by high operational pressure, even minor gaps in access management or oversight can lead to serious consequences. From the perspective of globally operating organizations, IT outsourcing should not be treated solely as a way to reduce costs or increase operational efficiency. It is increasingly becoming a component of a broader data security and digital risk management strategy. In practice, this means the need to consciously design cooperation models, clearly define responsibilities, and implement mechanisms that provide real control over access to systems and data, regardless of where and by whom they are processed. 8. Why it is worth working with TTMS in the area of IT outsourcing Secure IT outsourcing is not only a matter of technical competences. Equally important is the approach to risk management, access control, and shared responsibility on both sides of the cooperation. TTMS supports globally operating organizations in building outsourcing models that are scalable and efficient while at the same time providing real control over the security of data and systems. By working with TTMS, companies gain a partner that understands that digital security does not begin at the moment of incident response. It starts much earlier, at the stage of designing processes, roles, and scopes of responsibility. That is why in practice we place strong emphasis on precisely defining access rights, logically segmenting sensitive processes, and ensuring operational transparency that allows clients to continuously understand how their data and systems are being used. TTMS acts as a global partner that combines experience in building outsourcing teams with a practical approach to cybersecurity and regulatory compliance. Our goal is to create cooperation models that support business growth instead of generating hidden operational risks. If IT outsourcing is to be a stable foundation for growth, the key factor becomes choosing a partner for whom data security is an integral part of daily work, not an add-on to the service offering. Zapraszamy do kontaktu z TTMS, aby porozmawiać o modelu outsourcingu IT dopasowanym do rzeczywistych potrzeb biznesowych oraz wyzwań związanych z bezpieczeństwem cyfrowym. Does IT outsourcing to third countries increase the risk of data misuse? Outsourcing IT can increase the risk of data misuse if an organization loses real control over system access and how it is used. The location of the team, for example in India, is not the deciding factor in the level of risk. What matters most is how permissions are granted, user activity monitoring, and ongoing operational oversight. In practice, a well-designed collaboration model can be more secure than local teams operating without clear access control rules. Why social engineering threats are significant in IT outsourcing? Social engineering threats play a major role in IT outsourcing because many incidents are not based on technical vulnerabilities in systems. Far more often, they exploit legitimate access, knowledge of procedures, and the predictability of operational processes. Working according to repetitive patterns and high pressure for efficiency make employees susceptible to manipulation. Under such conditions, an attack does not need to look like a break-in to be effective. Which areas of IT outsourcing are most vulnerable to digital threats? The greatest risk concerns areas where access to systems and data is essential for daily work. These include technical support teams, particularly first and second line, which have contact with production systems and user data. Quality control teams working in test environments also show high vulnerability, where data very similar to production data is often used. Administrative processes related to customer service also remain a significant risk point. Are security certificates enough to protect data? Security certificates are an important element in building trust and confirming compliance with specific standards. However, they do not replace day-to-day operational practice. Real data security depends on how access is granted, how user activity is monitored, and whether the organization has ongoing visibility into what is happening in the systems. Without these elements, certificates remain a formal safeguard that does not always protect against real incidents. How to reduce digital security risk in outsourcing IT? Risk reduction begins with conscious management of access to data and systems. This includes both permission segmentation and regular reviews of who is using resources and to what extent. Continuous activity monitoring and clear assignment of responsibility between client and supplier are also crucial. Increasingly, organizations are also implementing an approach based on zero trust, which assumes verification of every access regardless of user location and role.
ReadBiggest 10 IT Problems in Business with Solutions for 2026
An IT outage can cost a business hundreds of thousands of dollars per hour, while cyberattacks now target companies of every size and industry. These realities show how critical IT problems in business have become. In 2026, technology is no longer just a support function. It directly affects security, scalability, compliance, and long-term competitiveness. Understanding IT problems in business today, along with practical solutions, is essential for leaders who want to protect growth and avoid costly disruptions. These common it problems in business are no longer isolated incidents. Real it problems in business examples from global organizations show how quickly technology gaps can impact revenue, security, and operational continuity. 1. Cybersecurity Threats and Data Breaches Cybersecurity remains the most serious IT issue in business. Ransomware, phishing, supply chain attacks, and data leaks affect organizations across all sectors. Attackers increasingly use automation and AI to exploit vulnerabilities faster than internal teams can react. Even one successful breach can result in financial losses, operational downtime, regulatory penalties, and long-term reputational damage. The solution requires a layered security approach. Businesses should combine endpoint protection, network monitoring, regular patching, and strong access control with ongoing employee awareness training. Multi-factor authentication, least-privilege access, and clearly defined incident response procedures significantly reduce risk. Cybersecurity must be treated as a continuous process, not a one-time project. 2. Remote and Hybrid Work IT Challenges Remote and hybrid work models introduce new IT related issues in business. Employees rely on secure remote access, stable connectivity, and collaboration tools, often from uncontrolled home environments. VPN instability, inconsistent device standards, and limited visibility into remote endpoints create operational and security risks. To address these challenges, organizations should standardize remote work infrastructure. Secure access solutions, device management platforms, and cloud-based collaboration tools are essential. Clear policies for remote security, combined with responsive IT support, help ensure productivity without compromising data protection. 3. Rapid Technology Change and AI Adoption The speed of technological change is one of the most complex IT issues and challenges for business. Companies face pressure to adopt AI, automation, analytics, and cloud-native solutions, often without fully modernized systems. Poor integration and unclear strategy can turn innovation into technical debt. Effective solutions start with alignment between technology initiatives and business objectives. Pilot projects, phased rollouts, and realistic roadmaps reduce risk. Organizations should modernize core systems where needed and invest in skills development to ensure teams can use new technologies effectively. 4. Data Privacy and Regulatory Compliance Data privacy regulations continue to expand globally, making compliance a major IT problem in business today. Managing personal and sensitive data across multiple systems increases the risk of non-compliance, fines, and customer trust erosion. Businesses should implement clear data governance frameworks, enforce access controls, and use encryption for data at rest and in transit. Regular audits, policy updates, and employee education help maintain compliance while still enabling data-driven operations. 5. IT Talent Shortages and Skills Gaps The lack of skilled IT professionals is a growing constraint for many organizations. Cybersecurity, cloud architecture, AI, and system integration expertise are in particularly short supply. This talent gap slows projects, increases operational risk, and places excessive pressure on existing teams. Solutions include upskilling internal staff, adopting flexible hiring models, and using external IT partners to supplement internal capabilities. Managed services and staff augmentation provide access to specialized skills without long-term hiring risk. 6. Legacy Systems and Outdated Infrastructure Legacy systems remain one of the most common IT problems in business examples. Outdated software and hardware are costly to maintain, difficult to secure, and incompatible with modern tools. They often limit scalability and innovation. A structured modernization strategy is essential. Organizations should assess system criticality, plan phased migrations, and replace unsupported technologies. Hybrid approaches, combining temporary integrations with long-term replacement plans, reduce disruption while enabling progress. 7. Cloud Complexity and Cost Control Cloud adoption has introduced new IT issues in business related to governance and cost management. Poor visibility into usage, overprovisioned resources, and fragmented environments lead to unnecessary spending and operational complexity. Cloud governance frameworks, usage monitoring, and cost optimization practices help regain control. Clear provisioning rules, automation, and regular reviews ensure that cloud investments support business outcomes rather than inflate budgets. 8. Backup, Disaster Recovery, and Business Continuity Inadequate backup and disaster recovery planning remains a serious IT problem in business today. Hardware failures, cyber incidents, or human error can lead to extended downtime and permanent data loss. Reliable backup strategies, offsite storage, and regularly tested recovery plans are critical. Businesses should define recovery objectives and ensure that both data and systems can be restored quickly under real-world conditions. 9. Poor System Integration and Data Silos Disconnected systems create inefficiencies and limit visibility across the organization. Data silos are a common IT related issue in business, forcing manual workarounds and reducing decision accuracy. Integration platforms, APIs, and unified data strategies help synchronize systems and eliminate duplication. Integration should be treated as a strategic capability, not an afterthought. 10. Performance Issues and Downtime Slow systems and frequent downtime directly reduce productivity and customer satisfaction. Aging hardware, overloaded networks, and insufficient monitoring contribute to these IT problems in business. Proactive maintenance, performance monitoring, and planned hardware refresh cycles help maintain reliability. Investing in scalable infrastructure and redundancy minimizes disruption and supports growth. Turn IT Problems into Business Advantages with TTMS When analyzing it problems and solutions in a business, leaders increasingly recognize that it issues and challenges for business are tightly connected to strategy, talent, and long-term scalability rather than technology alone. IT problems and solutions in a business are closely connected. With the right expertise and strategy, technology challenges can become drivers of efficiency, security, and growth. TTMS supports organizations worldwide in addressing IT issues in business through tailored managed services, system modernization, cloud optimization, cybersecurity, and IT consulting. By combining deep technical expertise with a strong understanding of business needs, TTMS helps companies reduce risk, improve performance, and prepare their IT environments for the demands of 2026 and beyond. To start addressing these challenges with expert support, contact us and explore how TTMS can help align your IT strategy with your business goals for 2026 and beyond. FAQ What are the major IT problems in business today? The major IT problems in business today include cybersecurity threats, remote work challenges, data privacy compliance, legacy systems, cloud cost management, and shortages of skilled IT professionals. These issues affect operational stability, security, and long-term competitiveness. What are the challenges of information technology in business? The challenges of information technology in business include aligning IT with business strategy, managing rapid technological change, protecting data, maintaining system reliability, and ensuring employees can effectively use digital tools. These challenges require both technical and organizational solutions. What is the biggest challenge facing the IT industry today? The biggest challenge facing the IT industry today is balancing innovation with security and reliability. As new technologies such as AI and automation emerge, organizations must adopt them responsibly while protecting systems, data, and users from increasing threats. How do businesses typically solve common IT problems? Businesses solve common IT problems through proactive maintenance, skilled IT support, clear governance policies, and the use of external experts when needed. Many organizations rely on managed services and consulting partners to address complex or resource-intensive challenges. What are examples of IT issues in business for remote teams? Examples of IT issues in business for remote teams include secure access management, device security, collaboration tool reliability, data protection outside the office, and remote user support. Addressing these issues requires secure infrastructure, clear policies, and responsive IT services.
ReadLLM Observability: How to Monitor AI When It Thinks in Tokens
Modern AI systems, especially large language models (LLMs), operate in a fundamentally different way than traditional software. They “think” in tokens (subunits of language), generating responses probabilistically. For business leaders deploying LLM-powered applications, this introduces new challenges in monitoring and reliability. LLM observability has emerged as a key practice to ensure these AI systems remain trustworthy, efficient, and safe in production. In this article, we’ll break down what LLM observability means, why it’s needed, and how to implement it in an enterprise setting. 1. What is LLM Observability (and Why Traditional Monitoring Falls Short)? In classical IT monitoring, we track servers, APIs, or microservices for uptime, errors, and performance. But an LLM is not a standard service – it’s a complex model that can fail in nuanced ways even while infrastructure looks healthy. LLM observability refers to the practice of tracking, measuring, and understanding how an LLM performs in production by linking its inputs, outputs, and internal behavior. The goal is to know why the model responded a certain way (or failed to) – not just whether the system is running. Traditional logging and APM (application performance monitoring) tools weren’t built for this. They might tell you a request to the model succeeded with 200 OK and took 300 ms, but they can’t tell if the answer was correct or appropriate. For example, an AI customer service bot could be up and responding quickly, yet consistently giving wrong or nonsensical answers – traditional monitors would flag “all green” while users are getting bad info. This is because classic tools focus on system metrics (CPU, memory, HTTP errors), whereas LLM issues often lie in the content of responses (e.g. factual accuracy or tone). In short, standard monitoring answers “Is the system up?”; LLM observability answers “Why did we get this output?”. Key differences include depth and context. LLM observability goes deeper by connecting inputs, outputs, and internal processing to reveal root causes. It might capture which user prompt led to a failure, what intermediate steps the model took, and how it decided on a response. It also tracks AI-specific issues like hallucinations or bias, and correlates model behavior with business outcomes (like user satisfaction or cost). Traditional monitoring can spot a crash or latency spike, but it cannot explain why a particular answer was wrong or harmful. With LLMs, we need a richer form of telemetry that illuminates the model’s “thought process” in order to manage it effectively. 2. New Challenges to Monitor: Hallucinations, Toxicity, Inconsistency, Latency Deploying LLMs introduces failure modes and risks that never existed in traditional apps. Business teams must monitor for these emerging issues: Hallucinations (Fabricated Answers): LLMs may confidently generate information that is false or not grounded in any source. For example, an AI assistant might invent a policy detail or cite a non-existent study. Such hallucinations can mislead users or produce incorrect business outputs. Observability tools aim to detect when answers “drift from verified sources”, so that fabricated facts can be caught and corrected. Often this involves evaluating response factuality (comparing against databases or using a secondary model) and flagging high “hallucination scores” for review. Toxic or Biased Content: Even well-trained models can occasionally output offensive, biased, or inappropriate language. Without monitoring, a single toxic response can reach customers and harm your brand. LLM observability means tracking the sentiment and safety of outputs – for instance, using toxicity classifiers or keyword checks – and escalating any potentially harmful content. If the AI starts producing biased recommendations or off-color remarks, observability alerts your team so they can intervene (or route those cases for human review). Inconsistencies and Drift: In multi-turn interactions, LLMs might contradict themselves or lose track of context. An AI agent might give a correct answer one minute and a confusing or opposite answer the next, especially if the conversation is long. These inconsistencies can frustrate users and degrade trust. Monitoring conversation traces helps spot when the model’s answers diverge or when it forgets prior context (a sign of context drift). By logging entire sessions, teams can detect if the AI’s coherence is slipping – e.g. it starts to ignore earlier instructions or change its tone unexpectedly – and then adjust prompts or retraining data as needed. Latency and Performance Spikes: LLMs are computationally heavy, and response times can vary with load, prompt length, or model complexity. Business leaders should track latency not just as an IT metric, but as a user-experience metric tied to quality. Interesting new metrics have emerged, like Time to First Token (TTFT) – how long before the AI starts responding – and tokens per second throughput. A slight delay might correlate with better answers (if the model is doing more reasoning), or it could indicate a bottleneck. By monitoring latency alongside output quality, you can find the sweet spot for performance. For example, if the 95th percentile TTFT jumps above 2 seconds, your dashboard would flag it and SREs could investigate whether a model update or a GPU issue is causing slowdowns. Ensuring prompt responses isn’t just an IT concern; it’s about keeping end-users engaged and satisfied. These are just a few examples. Other things like prompt injection attacks (malicious inputs trying to trick the AI), excessive token usage (which can drive up API costs), or high error/refusal rates are also important to monitor. The bottom line is that LLMs introduce qualitatively new angles to “failure” – an answer can be wrong or unsafe even though no error was thrown. Observability is our early warning system for these AI-specific issues, helping maintain reliability and trust in the system. 3. LLM Traces: Following the AI’s Thought Process (Token by Token) One of the most powerful concepts in LLM observability is the LLM trace. In microservice architectures, we use distributed tracing to follow a user request across services (e.g., a trace shows Service A calling Service B, etc., with timing). For LLMs, we borrow this idea to trace a request through the AI’s processing steps – essentially, to follow the model’s “thought process” across tokens and intermediate actions. An LLM trace is like a story of how an AI response was generated. It can include: the original user prompt, any system or context prompts added, the model’s raw output text, and even step-by-step reasoning if the AI used tools or an agent framework. Rather than a simple log line, a trace ties together all the events and decisions related to a single AI task. For example, imagine a user asks an AI assistant a question that requires a database lookup. A trace might record: the user’s query, the augmented prompt with retrieved data, the model’s first attempt and the follow-up call it triggered to an external API, the final answer, and all timestamps and token counts along the way. By connecting all related events into one coherent sequence, we see not just what the AI did, but how long each step took and where things might have gone wrong. Crucially, LLM traces operate at the token level. Since LLMs generate text token-by-token, advanced observability will log tokens as they stream out (or at least the total count of tokens used). This granular logging has several benefits. It allows you to measure costs (which are often token-based for API usage) per request and attribute them to users or features. It also lets you pinpoint exactly where in a response a mistake occurred – e.g., “the model was fine until token 150, then it started hallucinating.” With token-level timestamps, you can even analyze if certain parts of the output took unusually long (possibly indicating the model was “thinking” harder or got stuck). Beyond tokens, we can gather attention-based diagnostics – essentially peeking into the black box of the model’s neural network. While this is an emerging area, some techniques (often called causal tracing) try to identify which internal components (neurons or attention heads) were most influential in producing a given output. Think of it as debugging the AI’s brain: for a problematic answer, engineers could inspect which part of the model’s attention mechanism caused it to mention, say, an irrelevant detail. Early research shows this is possible; for instance, by running the model with and without certain neurons active, analysts can see if that neuron was “causally” responsible for a hallucination. While such low-level tracing is quite technical (and not usually needed for day-to-day ops), it underscores a key point: observability isn’t just external metrics, it can extend into model internals. Practically speaking, most teams will start with higher-level traces: logging each prompt and response, capturing metadata like model version, parameters (temperature, etc.), and whether the response was flagged by any safety filters. Each of these pieces is like a span in a microservice trace. By stitching them together with a trace ID, you get a full picture of an AI transaction. This helps with debugging (you can replay or simulate the exact scenario that led to a bad output) and with performance tuning (seeing a “waterfall” of how long each stage took). For example, a trace might reveal that 80% of the total latency was spent retrieving documents for a RAG (retrieval-augmented generation) system, versus the model’s own inference time – insight that could lead you to optimize your retrieval or caching strategy. In summary, “traces” for LLMs serve the same purpose as in complex software architectures: they illuminate the path of execution. When an AI goes off track, the trace is your map to figure out where and why. As one AI observability expert put it, structured LLM traces capture every step in your AI workflow, providing critical visibility into both system health and output quality. 4. Bringing AI into Your Monitoring Stack (Datadog, Kibana, Prometheus, etc.) How do we actually implement LLM observability in practice? The good news is you don’t have to reinvent the wheel; many existing observability tools are evolving to support AI use cases. You can often integrate LLM monitoring into the tools and workflows your team already uses, from enterprise dashboards like Datadog and Kibana to open-source solutions like Prometheus/Grafana. Datadog Integration: Datadog (a popular monitoring SaaS platform) has introduced features for LLM observability. It allows end-to-end tracing of AI requests alongside your usual application traces. For example, Datadog can capture each prompt and response as a span, log token usage and latency, and even evaluate outputs for quality or safety issues. This means you can see an AI request in the context of a user’s entire journey. If your web app calls an LLM API, the Datadog trace will show that call in sequence with backend service calls, with visibility into the prompt and result. According to Datadog’s product description, their LLM Observability provides “tracing across AI agents with visibility into inputs, outputs, latency, token usage, and errors at each step”. It correlates these LLM traces with APM data, so you could, for instance, correlate a spike in model error rate with a specific deploy on your microservice side. For teams already using Datadog, this integration means AI can be monitored with the same rigor as the rest of your stack – alerts, dashboards, and all. Elastic Stack (Kibana) Integration: If your organization uses the ELK/Elastic Stack for logging and metrics (Elasticsearch, Logstash, Kibana), you can extend it to LLM data. Elastic has developed an LLM observability module that collects prompts and responses, latency metrics, and safety signals into your Elasticsearch indices. Using Kibana, you can then visualize things like how many queries the LLM gets per hour, what the average response time is, and how often certain risk flags occur. Pre-configured dashboards might show model usage trends, cost stats, and content moderation alerts in one view. Essentially, your AI application becomes another source of telemetry fed into Elastic. One advantage here is the ability to use Kibana’s powerful search on logs – e.g. quickly filter for all responses that contain a certain keyword or all sessions from a specific user where the AI refused to answer. This can be invaluable for root cause analysis (searching logs for patterns in AI errors) and for auditing (e.g., find all cases where the AI mentioned a regulated term). Prometheus and Custom Metrics: Many engineering teams rely on Prometheus for metrics collection (often paired with Grafana for dashboards). LLM observability can be implemented here by emitting custom metrics from your AI service. For example, your LLM wrapper code could count tokens and expose a metric like llm_tokens_consumed_total or track latency in a histogram metric llm_response_latency_seconds. These metrics get scraped by Prometheus just like any other. Recently, new open-source efforts such as llm-d (a project co-developed with Red Hat) provide out-of-the-box metrics for LLM workloads, integrated with Prometheus and Grafana. They expose metrics like TTFT, token generation rate, and cache hit rates for LLM inference. This lets SREs set up Grafana dashboards showing, say, 95th percentile TTFT over the last hour, or cache hit ratio for the LLM context cache. With standard PromQL queries you can also set alerts: e.g., trigger an alert if llm_response_latency_seconds_p95 > 5 seconds for 5 minutes, or if llm_hallucination_rate (if you define one) exceeds a threshold. The key benefit of using Prometheus is flexibility – you can tailor metrics to what matters for your business (whether that’s tracking prompt categories, count of inappropriate content blocked, etc.) and leverage the robust ecosystem of alerting and Grafana visualization. The Red Hat team noted that traditional metrics alone aren’t enough for LLMs, so extending Prometheus with token-aware metrics fills the observability gap. Beyond these, other integrations include using OpenTelemetry – an open standard for traces and metrics. Many AI teams instrument their applications with OpenTelemetry SDKs to emit trace data of LLM calls, which can be sent to any backend (whether Datadog, Splunk, Jaeger, etc.). In fact, OpenTelemetry has become a common bridge: for example, Arize (an AI observability platform) uses OpenTelemetry so that you can pipe traces from your app to their system without proprietary agents. This means your developers can add minimal instrumentation and gain both in-house and third-party observability capabilities. Which signals should business teams track? We’ve touched on several already, but to summarize, an effective LLM monitoring setup will track a mix of performance metrics (latency, throughput, request rates, token usage, errors) and quality metrics (hallucination rate, factual accuracy, relevance, toxicity, user feedback). For instance, you might monitor: Average and p95 response time (to ensure SLAs are met). Number of requests per day (usage trends). Token consumption per request and total (for cost management). Prompt embeddings or categories (to see what users are asking most, and detect shifts in input type). Success vs failure rates – though “failure” for an LLM might mean the model had to fall back or gave an unusable answer, which you’d define (could be flagged via user feedback or automated evals). Content moderation flags (how often the model output was flagged or had to be filtered for policy). Hallucination or correctness score – possibly derived by an automated evaluation pipeline (for example, cross-checking answers against a knowledge base or using an LLM-as-a-judge to score factuality). This can be averaged over time and spiking values should draw attention. User satisfaction signals – if your app allows users to rate answers or if you track whether the user had to rephrase their query (which might indicate the first answer wasn’t good), these are powerful observability signals as well. By integrating these into familiar tools like Datadog dashboards or Kibana, business leaders get a real-time pulse of their AI’s performance and behavior. Instead of anecdotes or waiting for something to blow up on social media, you have data and alerts at your fingertips. 5. The Risks of Poor LLM Observability What if you deploy an LLM system and don’t monitor it properly? The enterprise risks are significant, and often not immediately obvious until damage is done. Here are the major risk areas if LLM observability is neglected. 5.1 Compliance and Legal Risks AI that produces unmonitored output can inadvertently violate regulations or company policies. For example, a financial chatbot might give an answer that constitutes unlicensed financial advice or an AI assistant might leak personal data from its training set. Without proper logs and alerts, these incidents could go unnoticed until an audit or breach occurs. The inability to trace model outputs to their inputs is also a compliance nightmare – regulators expect auditability. As Elastic’s AI guide notes, if an AI system leaks sensitive data or says something inappropriate, the consequences can range from regulatory fines to serious reputational damage, “impacting the bottom line.” Compliance teams need observability data (like full conversation records and model version history) to demonstrate due diligence and investigate issues. If you can’t answer “who did the model tell what, and why?” you expose the company to lawsuits and penalties. 5.2 Brand Reputation and Trust Hallucinations and inaccuracies, especially if frequent or egregious, will erode user trust in your product. Imagine an enterprise knowledge base AI that occasionally fabricates an answer about your company’s product – customers will quickly lose faith and might even question your brand’s credibility. Or consider an AI assistant that accidentally outputs offensive or biased content to a user; the PR fallout can be severe. Without observability, these incidents might be happening under the radar. You don’t want to find out from a viral tweet that your chatbot gave someone an insulting reply. Proactive monitoring helps catch harmful outputs internally before they escalate. It also allows you to quantify and report on your AI’s quality (for instance, “99.5% of responses this week were on-brand and factual”), which can be a competitive differentiator. In contrast, ignoring LLM observability is like flying blind – small mistakes can snowball into public disasters that tarnish your brand. 5.3 Misinformation and Bad Decisions If employees or customers are using an LLM thinking it’s a reliable assistant, any unseen increase in errors can lead to bad decisions. An unmonitored LLM could start giving subtly wrong recommendations (say an internal sales AI starts suggesting incorrect pricing or a medical AI gives slightly off symptom advice). These factual errors can propagate through the business or customer base, causing real-world mistakes. Misinformation can also open the company to liability if actions are taken based on the AI’s false output. By monitoring correctness (through hallucination rates or user feedback loops), organizations mitigate the risk of wrong answers going unchecked. Essentially, observability acts as a safety net – catching when the AI’s knowledge or consistency degrades so you can retrain or fix it before misinformation causes damage. 5.4 Operational Inefficiency and Hidden Costs LLMs that aren’t observed can become inefficient or expensive without anyone noticing immediately. For example, if prompts slowly grow longer or users start asking more complex questions, the token usage per request might skyrocket (and so do API costs) without clear visibility. Or the model might begin to fail at certain tasks, causing employees to spend extra time double-checking its answers (degrading productivity). Lack of monitoring can also lead to redundant usage – e.g., multiple teams unknowingly hitting the same model endpoint with similar requests, wasting computation. With proper observability, you can track token spend, usage patterns, and performance bottlenecks to optimize efficiency. Unobserved AI often means money left on the table or spent in the wrong places. In a sense, observability pays for itself by highlighting optimization opportunities (like where a cache could cut costs, or identifying that a cheaper model could handle 30% of the requests currently going to an expensive model). 5.5 Stalled Innovation and Deployment Failure There’s a more subtle but important risk: without observability, AI projects can hit a wall. Studies and industry reports note that many AI/ML initiatives fail to move from pilot to production, often due to lack of trust and manageability. If developers and stakeholders can’t explain or debug the AI’s behavior, they lose confidence and may abandon the project (the “black box” fear). For enterprises, this means wasted investment in AI development. Poor observability can thus directly lead to project cancellation or shelved AI features. On the flip side, having good monitoring and tracing in place gives teams the confidence to scale AI usage, because they know they can catch issues early and continuously improve the system. It transforms AI from a risky experiment to a reliable component of operations. As Splunk’s analysts put it, failing to implement LLM observability can have serious consequences – it’s not just optional, it’s a competitive necessity. In summary, ignoring LLM observability is an enterprise risk. It can result in compliance violations, brand crises, uninformed decisions, runaway costs, and even the collapse of AI projects. Conversely, robust observability mitigates these risks by providing transparency and control. You wouldn’t deploy a new microservice without logs and monitors; deploying an AI model without them is equally perilous – if not more so, given AI’s unpredictable nature. 6. How Monitoring Improves Trust, ROI, and Agility Now for the good news: when done right, LLM observability doesn’t just avoid negatives – it creates significant positives for the business. By monitoring the quality and safety of AI outputs, organizations can boost user trust, maximize ROI on AI, and accelerate their pace of innovation. Strengthening User Trust and Adoption: Users (whether internal employees or external customers) need to trust your AI tool to use it effectively. Each time the model gives a helpful, correct answer, trust is built; each time it blunders, trust is chipped away. By monitoring output quality continuously, you ensure that you catch and fix issues before they become endemic. This leads to more consistent, reliable performance from the AI – which users notice. For instance, if you observe that the AI tends to falter on a certain category of questions, you can improve it (perhaps by fine-tuning on those cases or adding a fallback). The next time users ask those questions, the AI does better, and their confidence grows. Over time, a well-monitored AI system maintains a high level of trust, meaning users will actually adopt and rely on it. This is crucial for ROI – an AI that employees refuse to use because “it’s often wrong” provides little value. Monitoring is how you keep the AI’s promises to users. It’s analogous to quality assurance in manufacturing – you’re ensuring the product (AI responses) meets the standard consistently, thereby strengthening the trust in the “brand” of your AI. Protecting and Improving ROI: Deploying LLMs (especially large ones via API) can be expensive. Every token generated has a cost, and every mistake has a cost (in support time, customer churn, etc.). Observability helps maximize the return on this investment by both reducing waste and enhancing outcomes. For example, monitoring token usage might reveal that a huge number of tokens are spent on a certain type of query that could be answered with a smaller model or a cached result – allowing you to cut down costs. Or you might find through logs that users often ask follow-up questions for clarification, indicating the initial answers aren’t clear enough – a prompt tweak could resolve that, leading to fewer calls and a better user experience. Efficiency gains and cost control directly contribute to ROI, and they come from insights surfaced by observability. Moreover, by tracking business-centric metrics (like conversion rates or task completion rates with AI assistance), you can draw a line from AI performance to business value. If you notice that when the model’s accuracy goes up, some KPI (e.g., customer satisfaction or sales through a chatbot) also goes up, that’s demonstrating ROI on good AI performance. In short, observability data allows you to continually tune the system for optimal value delivery, rather than flying blind. It turns AI from a cost center into a well-measured value driver. Faster Iteration and Innovation: One of the less obvious but most powerful benefits of having rich observability is how it enables rapid improvement cycles. When you can see exactly why the model did something (via traces) and measure the impact of changes (via evaluation metrics), you create a feedback loop for continuous improvement. Teams can try a new prompt template or a new model version and immediately observe how metrics shift – did hallucinations drop? Did response time improve? – and then iterate again. This tight loop dramatically accelerates development compared to a scenario with no visibility (where you might deploy a change and just hope for the best). Monitoring also makes it easier to do A/B tests or controlled rollouts of new AI features, because you have the telemetry to compare outcomes. According to best practices, instrumentation and observability should be in place from day one, so that every experiment teaches you something. Companies that treat AI observability as a first-class priority will naturally out-iterate competitors who are scrambling in the dark. As one Splunk report succinctly noted, LLM observability is non-negotiable for production-grade AI – it “builds trust, keeps costs in check, and accelerates iteration.” With each iteration caught by observability, your team moves from reacting to issues toward proactively enhancing the AI’s capabilities. The end result is a more robust AI system, delivered faster. To put it simply, monitoring an AI system’s quality and safety is akin to having analytics on a business process. It lets you manage and improve that process. With LLM observability, you’re not crossing your fingers that the AI is helping your business – you have data to prove it and tools to improve it. This improves stakeholder confidence (executives love seeing metrics that demonstrate the AI is under control and benefiting the company) and paves the way for scaling AI to more use cases. When people trust that the AI is being closely watched and optimized, they’re more willing to invest in deploying it widely. Thus, good observability can turn a tentative pilot into a successful company-wide AI rollout with strong user and management buy-in. 7. Metrics and Alerts: Examples from the Real World What do LLM observability metrics and alerts look like in practice? Let’s explore a few concrete examples that a business might implement: Hallucination Spike Alert: Suppose you define a “hallucination score” for each response (perhaps via an automated checker that compares the AI’s answer to a knowledge base, or an LLM that scores factuality). You could chart the average hallucination score over time. If on a given day or hour the score shoots above a certain threshold – indicating the model is producing unusually inaccurate information – an alert would trigger. For instance, “Alert: Hallucination rate exceeded 5% in the last hour (threshold 2%)”. This prompt notification lets the team investigate immediately: maybe a recent update caused the model to stray, or maybe a specific topic is confusing it. Real-world case: Teams have set up pipelines where if an AI’s answers start deviating from trusted sources beyond a tolerance, it pages an engineer. As discussed earlier, logging full interaction traces can enable such alerts – e.g. Galileo’s observability platform allows custom alerts when conversation dynamics drift, like increases in hallucinations or toxicity beyond normal levels. Toxicity Filter Alert: Many companies run outputs through a toxicity or content filter (such as OpenAI’s moderation API or a custom model) before it reaches the user. You’d want to track how often the filter triggers. An example metric is “% of responses flagged for toxicity”. If that metric spikes (say it’s normally 0.1% and suddenly hits 1% of outputs), something’s wrong – either users are prompting sensitive topics more, or the model’s behavior changed. An alert might say “Content Policy Alerts increased tenfold today”, prompting a review of recent queries and responses. This kind of monitoring ensures you catch potential PR issues or policy violations early. It’s much better to realize internally that “hey, our AI is being prompted in a way that yields edgy outputs; let’s adjust our prompt or reinforce guardrails” than to have a user screenshot a bad output on social media. Proactive alerts give you that chance. Latency SLA Breach: We touched on Time to First Token (TTFT) as a metric. Imagine you have an internal service level agreement that 95% of user queries should receive a response within 2 seconds. You can monitor the rolling p95 latency of the LLM and set an alert if it goes beyond 2s for more than, say, 5 minutes. A real example from an OpenShift AI deployment: they monitor TTFT and have Grafana charts showing p95 and p99 TTFT; when it creeps up, it indicates a performance regression. The alert might read, “Degraded performance: 95th percentile response time is 2500ms (threshold 2000ms).” This pushes the ops team to check if a new model version is slow, or if there’s a spike in load, or maybe an upstream service (like a database used in retrieval) is lagging. Maintaining snappy performance is key for user engagement, so these alerts directly support user experience goals. Prompt Anomaly Detection: A more advanced example is using anomaly detection on the input prompts the AI receives. This is important for security – you want to know if someone is trying something unusual, like a prompt injection attack. Companies can embed detectors that analyze prompts for patterns like attempts to break out of role or include suspicious content. If a prompt is significantly different from the normal prompt distribution (for instance, a prompt that says “ignore all previous instructions and …”, which is a known attack pattern), the system can flag it. An alert might be “Anomalous prompt detected from user X – possible prompt injection attempt.” This could integrate with security incident systems. Observability data can also feed automated defenses: e.g., if a prompt looks malicious, the system might automatically refuse it and log the event. For the business, having this level of oversight prevents attacks or misuse from going unnoticed. As one observability guide noted, monitoring can help “find jailbreak attempts, context poisoning, and other adversarial inputs before they impact users.” In practice, this might involve an alert and also kicking off additional logging when such a prompt is detected (to gather evidence or forensics). Drift and Accuracy Trends: Over weeks and months, it’s useful to watch quality trends. For example, if you have an “accuracy score” from periodic evaluations or user feedback, you might plot that and set up a trend alert. “Alert: Model accuracy has dropped 10% compared to last month.” This could happen due to data drift (the world changed but your model hasn’t), or maybe a subtle bug introduced in a prompt template. A real-world scenario: say you’re an e-commerce company with an AI shopping assistant. You track a metric “successful recommendation rate” (how often users actually click on or like the recommendation the AI gave). If that metric starts declining over a quarter, an alert would notify product managers to investigate – perhaps the model’s suggestions became less relevant due to a change in inventory, signaling it’s time to retrain on newer data. Similarly, embedding drift (if you use vector embeddings for retrieval) can be tracked, and an alert can fire when embeddings of new content start veering far from the original training set’s distribution, indicating potential model drift. These are more strategic alerts, helping ensure the AI doesn’t silently become stale or less effective over time. Cost or Usage Spike: Another practical metric is cost or usage monitoring. You might have a budget for AI usage per month. Observability can include tracking of total tokens consumed (which directly correlate to cost if using a paid API) or hits to the model. If suddenly one feature or user starts using 5x the normal amount, an alert like “Alert: LLM usage today is 300% of normal – potential abuse or runaway loop” can save you thousands of dollars. In one incident (shared anecdotally in industry), a bug caused an AI agent to call itself in a loop, racking up a huge bill – robust monitoring of call rates could have caught that infinite loop after a few minutes. Especially when LLMs are accessible via APIs, usage spikes could mean either a successful uptake (which is good, but then you need to know to scale capacity or renegotiate API limits) or a sign of something gone awry (like someone hammering the API or a process stuck in a loop). Either way, you want alerts on it. These examples show that LLM observability isn’t just passive monitoring, it’s an active guardrail. By defining relevant metrics and threshold alerts, you essentially program the system to watch itself and shout out when something looks off. This early warning system can prevent minor issues from becoming major incidents. It also gives your team concrete, quantitative signals to investigate, rather than vague reports of “the AI seems off lately.” In an enterprise scenario, such alerts and dashboards would typically be accessible to not only engineers but also product managers and even risk/compliance officers (for things like content violations). The result is a cross-functional ability to respond quickly to AI issues, maintaining the smooth operation and trustworthiness of the AI in production. 8. Build vs. Buy: In-House Observability or Managed Solutions? As you consider implementing LLM observability, a strategic question arises: should you build these capabilities in-house using open tools, or leverage managed solutions and platforms? The answer may be a mix of both, depending on your resources and requirements. Let’s break down the options. 8.1 In-House (DIY) Observability This approach means using existing logging/monitoring infrastructure and possibly open-source tools to instrument your LLM applications. For example, your developers might add logging code to record prompts and outputs, push those into your logging system (Splunk, Elastic, etc.), and emit custom metrics to Prometheus for things like token counts and error rates. You might use OpenTelemetry libraries to generate standardized traces of each AI request, then export those traces to your monitoring backend of choice. The benefits of the in-house route include full control over data (important for sensitive contexts) and flexibility to customize what you track. You’re not locked into any vendor’s schema or limitations – you can decide to log every little detail if you want. There are also emerging open-source tools to assist, such as Langfuse (which provides an open-source LLM trace logging solution) or Phoenix (Arize’s open-source library for AI observability), which you can host yourself. However, building in-house requires engineering effort and expertise in observability. You’ll need people who understand both AI and logging systems to glue it all together, set up dashboards, define alerts, and maintain the pipelines. For organizations with strong devops teams and perhaps stricter data governance (e.g., banks or hospitals that prefer not to send data to third parties), in-house observability is often the preferred path. It aligns with using existing enterprise monitoring investments, just extending them to cover AI signals. 8.2 Managed Solutions and AI-Specific Platforms A number of companies now offer AI observability as a service or product, which can significantly speed up your implementation. These platforms come ready-made with features like specialized dashboards for prompt/response analysis, drift detection algorithms, built-in evaluation harnesses, and more. Let’s look at a few mentioned often: OpenAI Evals: This is an open-source framework (from OpenAI) for evaluating model outputs systematically. While not a full monitoring tool, it’s a valuable piece of the puzzle. With OpenAI Evals, you can define evaluation tests (evals) for your model – for example, check outputs against known correct answers or style guidelines – and run these tests periodically or on new model versions. Think of it as unit/integration tests for AI behavior. You wouldn’t use Evals to live-monitor every single response, but you could incorporate it to regularly audit the model’s performance on key tasks. It’s especially useful when considering model upgrades: you can run a battery of evals to ensure the new model is at least as good as the old on critical dimensions (factuality, formatting, etc.). If you have a QA team or COE (Center of Excellence) for AI, they might maintain a suite of evals. As a managed service, OpenAI provides an API and dashboard for evals if you use their platform, or you can run the open-source version on your own. The decision here is whether you want to invest in creating custom evals (which pays off in high-stakes use cases), or lean on more automated monitoring for day-to-day. Many enterprises do both: real-time monitoring catches immediate anomalies, while eval frameworks like OpenAI Evals provide deeper periodic assessment of model quality against benchmarks. Weights & Biases (W&B): W&B is well-known for ML experiment tracking, and they have extended their offerings to support LLM applications. With W&B, you can log prompts, model configurations, and outputs as part of experiments or production runs. They offer visualization tools to compare model versions and even some prompt management. For instance, W&B’s platform can track token counts, latencies, and even embed charts of attention or activation stats, linking them to specific model versions or dataset slices. One of the advantages of W&B is integration into the model development workflow – developers already use it during training or fine-tuning, so extending it to production monitoring feels natural. W&B can act as a central hub where your team checks both training metrics and live model metrics. However, it is a hosted solution (though data can be kept private), and it’s more focused on developer insights than business user dashboards. If you want something that product owners or ops engineers can also easily use, you might combine W&B with other tools. W&B is great for rapid iteration and experiment tracking, and somewhat less tailored to real-time alerting (though you can certainly script alerts via its API or use it in conjunction with, say, PagerDuty). Arize (AI Observability Platform): Arize is a platform specifically designed for ML monitoring, including LLMs. It provides a full suite: data drift detection, bias monitoring, embedding analysis, and tracing. One of Arize’s strengths is its focus on production – it can ingest predictions and outcomes from your models continuously and analyze them for issues. For LLMs, Arize introduced features like LLM tracing (capturing the chain of prompts and outputs) and evaluation with “LLM-as-a-Judge” (using models to score other models’ outputs). It also offers out-of-the-box dashboard widgets for things like hallucination rate, prompt failure rate, latency distribution, etc. A key point is that Arize builds on open standards like OpenTelemetry, so you can instrument your app to send trace data in a standard format and Arize will interpret it. If you prefer not to build your own analytics for embeddings and drift, Arize has those ready – for example, it can automatically highlight if the distribution of prompts today looks very different from last week (which might explain a model’s odd behavior). Another plus is the ability to set monitors in Arize that will alert you if, say, accuracy falls for a certain slice of data or if a particular failure mode (like a refusal to answer) suddenly increases. Essentially, it’s like a purpose-built AI control tower. The trade-off is cost and data considerations: you’ll be sending your model inferences and possibly some data to a third-party service. Arize emphasizes enterprise readiness (they highlight being vendor-neutral and allowing on-prem deployment for sensitive cases), which can ease some concerns. If your team is small or you want faster deployment, a platform like this can save a lot of time by providing a turnkey observability solution for AI. Aside from these, there are other managed tools and emerging startups (e.g., TruEra, Mona, Galileo etc.) focusing on aspects of AI quality monitoring, some of which specialize in NLP/LLMs. There are also open-source libraries like Trulens or Langchain’s debugging modules which can form part of an in-house solution. When to choose which? A heuristic: if your AI usage is already at scale or high stakes (e.g., user-facing in a regulated industry), leaning on a proven platform can accelerate your ability to govern it. These platforms embed a lot of best practices and will likely evolve new features (like monitoring for the latest prompt injection tricks) faster than an internal team could. On the other hand, if your use case is highly custom or you have stringent data privacy rules, an internal build on open tools might be better. Some companies start in-house but later integrate a vendor as their usage grows and they need more advanced analytics. In many cases, a hybrid approach works: instrument with open standards like OpenTelemetry so you have raw data that can feed multiple destinations. You might send traces to your in-house logging system and to a vendor platform simultaneously. This avoids lock-in and provides flexibility. For instance, raw logs might stay in Splunk for long-term audit needs, while summarized metrics and evaluations go to a specialized dashboard for the AI engineering team. The choice also depends on team maturity. If you have a strong MLOps or devops team interested in building these capabilities, the in-house route can be empowering and cost-effective. If not, leveraging a managed service (essentially outsourcing the heavy lifting of analysis and UI) can be well worth the investment to get observability right from the start. Regardless of approach, ensure that the observability plan is in place early in your LLM project. Don’t wait for the first major incident to cobble together logging. As a consultant might advise: treat observability as a core requirement, not a nice-to-have. It’s easier to build it in from the beginning than to retro-fit monitoring after an AI system has already been deployed and possibly misbehaving. Conclusion: Turning On the Lights for Your AI (Next Steps with TTMS) In the realm of AI, you can’t manage what you don’t monitor. LLM observability is how business leaders turn on the lights in the “black box” of AI, ensuring that when their AI thinks in tokens, those tokens are leading to the right outcomes. It transforms AI deployment from an act of faith into a data-driven process. As we’ve discussed, robust monitoring and tracing for LLMs yields safer systems, happier users, and ultimately more successful AI initiatives. It’s the difference between hoping an AI is working and knowing exactly why it succeeds or fails. For executives and decision-makers, the takeaway is clear: invest in LLM observability just as you would in security, quality assurance, or any critical operational facet. This investment will pay dividends in risk reduction, improved performance, and faster innovation cycles. It ensures your AI projects deliver value reliably and align with your enterprise’s standards and goals. If your organization is embarking on (or expanding) a journey into AI and LLM-powered solutions, now is the time to put these observability practices into action. You don’t have to navigate it alone. Our team at TTMS specializes in secure, production-grade AI deployments, and a cornerstone of that is implementing strong observability and control. We’ve helped enterprises set up the dashboards, alerts, and workflows that keep their AI on track and compliant with ease. Whether you need to audit an existing AI tool or build a new LLM application with confidence from day one, we’re here to guide you. Next Steps: We invite you to reach out and explore how to make your AI deployments trustworthy and transparent. Let’s work together to tailor an LLM observability strategy that fits your business – so you can scale AI with confidence, knowing that robust monitoring and safeguards are built in every step of the way. With the right approach, you can harness the full potential of large language models safely and effectively, turning cutting-edge AI into a reliable asset for your enterprise. Contact TTMS to get started on this journey toward secure and observable AI – and let’s ensure your AI thinks in tokens and acts in your best interest, every time.
ReadRecommended articles
The world’s largest corporations have trusted us
We hereby declare that Transition Technologies MS provides IT services on time, with high quality and in accordance with the signed agreement. We recommend TTMS as a trustworthy and reliable provider of Salesforce IT services.
TTMS has really helped us thorough the years in the field of configuration and management of protection relays with the use of various technologies. I do confirm, that the services provided by TTMS are implemented in a timely manner, in accordance with the agreement and duly.
Ready to take your business to the next level?
Let’s talk about how TTMS can help.

Monika Radomska
Sales Manager