Sort by topics
Best AI System for a Company in 2026
If you are deciding which AI system to buy for a company, start with a practical rule: buy the platform that already lives where your people work. For most enterprise, organisation, and company environments, the strongest choices are no longer standalone chatbots. They are AI systems tied to email, documents, meetings, files, permissions, automation, and analytics. That is why, in our assessment, Microsoft 365 with Copilot comes first, Google Workspace with Gemini comes second, and the rest of the market follows based on workflow depth, governance, and ecosystem fit. 1. What Makes the Best AI Platforms for Enterprise Work in 2026? The best ai platforms for enterprise work are the ones employees can adopt without having to rebuild the way the organisation already operates. In 2026, the buying question is less about which model looks best in a benchmark, and more about which platform can be governed, connected to company data, rolled out safely, and turned into repeatable work. Microsoft positions Copilot around Microsoft Graph, permissions, and the Microsoft 365 service boundary; Google now includes Gemini and NotebookLM directly in Workspace plans; and vendors like Salesforce, ServiceNow, Amazon, and SAP frame AI as a workflow layer, not just a chat tab. That shift is exactly why searches such as “best enterprise ai platforms 2026”, “best ai platforms for enterprise use”, and “what are the best enterprise ai platforms?” all need the same answer structure: first identify the operating environment, then the AI layer that fits it, then the delivery partner that can turn licences into measurable business change. 2. How we ranked the leading enterprise AI systems This ranking prioritises five factors: native fit with daily work, enterprise security and admin controls, ability to use company data with permissions, workflow automation depth, and ecosystem maturity. We also penalised platforms that are excellent as standalone assistants but weaker as a whole-company operating layer. For private companies such as OpenAI, some business metrics come from public reporting rather than annual filings, because no public annual report is available. 3. Our ranking of the best AI systems for companies 3.1 Microsoft 365 with Copilot, Copilot Chat, Copilot Studio, Power Platform, and Power BI context Microsoft is the best AI system to buy for a company if your organisation already runs on Outlook, Teams, Word, Excel, PowerPoint, SharePoint, and OneDrive. Microsoft 365 Copilot works inside those apps, uses grounding through Microsoft Graph in the user’s tenant, respects existing permissions, and keeps prompts, retrieved data, and responses inside the Microsoft 365 service boundary. Microsoft also lets organisations build and publish agents through Copilot Studio, and those agents can be added to Microsoft 365 Copilot. Copilot Chat is available to users with commercial Microsoft 365 licences, while the full Microsoft 365 Copilot licence unlocks deeper in-app Copilot experiences and broader agent scenarios. This is the strongest answer to the query “best ai platforms for enterprise use 2026” because Microsoft combines the everyday work surface, the security model, the data layer, and the automation layer in one stack. It is especially strong for companies that want one standard assistant across leadership, sales, finance, operations, HR, and project teams, rather than a patchwork of isolated tools. Microsoft: company snapshot Latest reported revenue: $281.7 billion in FY2025 Number of employees: 228,000+ Website: microsoft.com Headquarters: Redmond, Washington, United States Main services / focus: Microsoft 365, Copilot, Copilot Studio, Teams, SharePoint, Power Platform, Power BI, Azure AI, enterprise security and governance For Microsoft-first companies, TTMS deserves a direct mention as a delivery partner. TTMS states that it uses Microsoft 365 itself, offers Microsoft 365 training, process automation with Power Automate and Power Apps, M365 security hardening, Teams application development, and migrations from Linux, Google Suite, and on-prem solutions into Microsoft 365. TTMS also develops Power Apps and AI solutions integrated with Microsoft 365, Power BI, Dataverse, Teams, and SharePoint, including Azure OpenAI based document search and analysis with referenced sources. If your company wants Microsoft AI to become real workflow change rather than just another licence purchase, TTMS is genuinely relevant here. Relevant internal next step: Microsoft 365 services from TTMS and Power Apps and AI solutions from TTMS. 3.2 Google Workspace with Gemini and NotebookLM Google ranks second because it now offers one of the cleanest AI experiences for document-heavy and research-heavy organisations. Google Workspace plans include access to the Gemini app, NotebookLM, and Gemini in Gmail, Docs, Meet, and more. Google positions Gemini Enterprise as a secure platform where agents can work across Workspace apps, while NotebookLM has become a serious differentiator for teams that need to reason across PDFs, websites, slide decks, and shared internal knowledge. For many companies, Google is the best alternative to Microsoft rather than a niche option. If your teams live in Docs, Drive, Meet, and browser-centred workflows, Google gives you a low-friction route to everyday AI adoption. NotebookLM Enterprise also adds enterprise-oriented controls and security options, which matters for organisations that want structured knowledge workflows rather than open-ended prompting without guardrails. Google: company snapshot Latest reported revenue: $403 billion in FY2025 Number of employees: 190,820 Website: workspace.google.com Headquarters: Mountain View, California, United States Main services / focus: Google Workspace, Gemini, NotebookLM, Google Cloud AI, enterprise search and collaboration, agent workflows 3.3 OpenAI ChatGPT Enterprise OpenAI comes third because ChatGPT Enterprise is arguably the most powerful standalone enterprise assistant on the market, but it is still not the most natural whole-company operating layer for most buyers. OpenAI’s enterprise offer focuses on built-in apps and connectors for company data, including Microsoft SharePoint, GitHub, Google Drive, and Box, plus enterprise-grade security, admin controls, SAML SSO, data encryption, compliance support, and the explicit commitment that business data is not used to train its models by default for ChatGPT Business and Enterprise customers. That makes OpenAI one of the best enterprise generative ai platforms 2026, especially for organisations that want frontier capability, flexible connectors, strong reasoning, and a shared workspace without committing to a single broader productivity suite. It ranks behind Microsoft and Google mainly because most companies still need to do more integration, governance design, and workflow packaging around ChatGPT than around the two major workspace-native stacks. OpenAI: company snapshot Latest reported revenue: More than $20 billion annualized revenue in 2025, above $25 billion annualized by March 2026 Number of employees: Approx. 4,500 in March 2026 Website: openai.com Headquarters: San Francisco, California, United States Main services / focus: ChatGPT Enterprise, company connectors, advanced reasoning, deep research, admin controls, API platform 3.4 Salesforce Agentforce Salesforce ranks fourth because it is one of the most compelling AI systems for customer-facing work, but it is not the best first purchase for every department in the average organisation. Salesforce describes itself as the “#1 AI CRM” and positions Agentforce as the platform that brings humans, agents, unified data, and Customer 360 apps together. Its recent results also show meaningful traction, with Agentforce ARR reaching $800 million and 29,000 deals closed by the end of fiscal 2026. If customer operations are the centre of gravity in your company, Salesforce may rank even higher than this list suggests. It becomes especially powerful when service, sales, and internal collaboration already run through Salesforce and Slack. For a general search like “best ai platforms for enterprise use”, however, Salesforce sits behind Microsoft, Google, and OpenAI because its sweet spot is customer workflow reinvention rather than the entire everyday productivity layer. Salesforce: company snapshot Latest reported revenue: $41.5 billion in FY2026 Number of employees: 76,000+ Website: salesforce.com Headquarters: San Francisco, California, United States Main services / focus: Agentforce, AI CRM, Customer 360, Data 360 and Data Cloud, Slack, Tableau, sales and service workflows 3.5 ServiceNow AI Platform and Now Assist ServiceNow ranks fifth because it is outstanding for internal service workflows, IT, HR, and employee experience, but less universal than Microsoft or Google for content creation and day-to-day office work. ServiceNow describes its offer as the AI platform for business transformation, a trusted single platform, data model, and system of action. Now Assist is the generative AI layer on top, designed to improve productivity through conversation, summaries, proactive experiences, and workflow-specific skills. That makes ServiceNow one of the best enterprise AI platforms for organisations whose biggest pain points are ticketing, case handling, employee support, approvals, and process orchestration. If your company wants AI to improve internal service delivery rather than reinvent writing, meetings, and documents first, ServiceNow is a very strong buy. ServiceNow: company snapshot Latest reported revenue: $13.278 billion in 2025 Number of employees: 29,187 Website: servicenow.com Headquarters: Santa Clara, California, United States Main services / focus: AI Platform, Now Assist, IT workflows, HR and employee experience, service operations, workflow automation 3.6 Amazon Q Business Amazon Q Business ranks sixth and is especially compelling for AWS-native companies. Amazon describes it as a generative AI powered assistant for finding information, gaining insight, and taking action at work. It provides permission-aware responses with citations, connects to enterprise content and systems, supports plugins and actions across third-party tools, and can be accessed through integrations such as Slack, Outlook, Word, and Teams. Amazon also offers Q Apps and workflow automation capabilities around the product. Amazon Q Business is not as naturally embedded into a full office suite as Microsoft or Google, which is why it ranks lower for a generic “best ai system to buy for a company” query. But for organisations already standardised on AWS, or those that care deeply about permissions-aware retrieval, citations, and action-taking across complex systems, Amazon Q is a serious enterprise platform rather than a side tool. Amazon: company snapshot Latest reported revenue: $716.9 billion company-wide in 2025, with AWS segment sales of $128.7 billion Number of employees: 1,576,000+ Website: aws.amazon.com Headquarters: Seattle, Washington, United States Main services / focus: AWS, Amazon Q Business, enterprise search and insights, knowledge assistants, workflow actions, cloud infrastructure 3.7 SAP Business AI with Joule SAP takes the seventh position, but it can move much higher in SAP-first enterprises. Joule is SAP’s AI assistant and the company frames SAP Business AI around role-based assistants and agents connected to finance, procurement, HR, supply chain, customer experience, and business transformation processes. SAP also emphasises a unified AI experience across SAP and non-SAP systems, plus ready-made agents and new agent-building capabilities in Joule Studio. For a company that already runs core operations on SAP, this can be one of the best ai platforms for enterprise work because it is grounded in the business process layer that matters most. For a company looking for its first broad productivity assistant across email, meetings, and files, SAP is less universal than Microsoft or Google, which is why it sits lower in this overall ranking. SAP: company snapshot Latest reported revenue: €36.8 billion in FY2025 Number of employees: 110,000+ Website: sap.com Headquarters: Walldorf, Germany Main services / focus: SAP Business AI, Joule, ERP and finance workflows, procurement, HR, supply chain, enterprise agents and business data Bottom line: for most company buyers, Microsoft is the best AI system to buy if you need broad adoption across the whole organisation. Google is the best challenger if your workday already runs in Workspace. OpenAI is the strongest standalone enterprise assistant. Salesforce, ServiceNow, Amazon, and SAP become especially compelling when your business value is concentrated in CRM, service workflows, AWS-native knowledge work, or SAP-centred operations. 4. Best Enterprise AI Platforms in 2026 – Comparison Table Platform Best for Main strength Potential limitation Best fit company type Microsoft 365 Copilot Enterprise productivity and collaboration Deep integration with Teams, Outlook, Word, Excel, SharePoint, Power Platform, and Power BI Requires mature Microsoft 365 environment and governance Large and mid-sized organisations using Microsoft ecosystem Google Workspace + Gemini Research-heavy and document-centric work Strong AI experience in Docs, Gmail, Meet, and NotebookLM Less process automation depth than Microsoft stack Google Workspace-first companies and distributed teams OpenAI ChatGPT Enterprise Advanced reasoning and general-purpose AI assistance Very strong generative AI capabilities and flexible connectors Requires more integration and governance planning Innovation-focused organisations and AI-first teams Salesforce Agentforce Customer operations and CRM workflows AI embedded into Customer 360 and sales/service operations Less universal outside customer-facing departments Sales-driven and service-driven enterprises ServiceNow AI Platform Internal workflows and employee support Excellent workflow automation for IT, HR, and operations Not designed as a broad productivity suite Process-heavy organisations with large support operations Amazon Q Business AWS-native enterprise environments Permission-aware enterprise search and AI actions Smaller collaboration ecosystem than Microsoft or Google Cloud-native companies using AWS infrastructure SAP Business AI ERP and operational workflows Strong integration with finance, procurement, and supply chain Less useful outside SAP-centric environments Large enterprises running SAP ecosystems 5. How to Choose the Best Enterprise AI Platform for Your Company The best enterprise AI platform depends less on model popularity and more on where your organisation already works. Companies built around Microsoft 365, Teams, SharePoint, and Power Platform will usually benefit most from Microsoft Copilot and the broader Microsoft AI ecosystem. Google Workspace-first organisations often gain faster adoption from Gemini and NotebookLM. Businesses focused on CRM and customer operations may prefer Salesforce Agentforce, while SAP-centric enterprises typically achieve the strongest results from SAP Business AI. Before buying any enterprise AI system, companies should evaluate three areas: where daily work happens, where sensitive company data lives, and whether the goal is a company-wide assistant, workflow automation, or domain-specific AI agents. Many failed AI rollouts happen because organisations choose tools based on hype instead of operational fit, governance readiness, and ecosystem compatibility. 6. Why Microsoft comes first and where TTMS fits When buyers ask “what are the best enterprise ai platforms?”, they often mix up three categories: everyday work assistants, agent builders, and workflow systems. Microsoft currently covers all three more coherently than anyone else for the average enterprise buyer. It has the daily work surface in Microsoft 365, enterprise data grounding through Microsoft Graph, agent creation in Copilot Studio, and adjacent process and analytics layers in Power Platform and Power BI. That breadth is why it is the safest first recommendation for a company that wants one strategic AI standard rather than a bundle of separate tools. TTMS fits naturally into that Microsoft story because its offer is not just advisory. TTMS highlights adoption support, tailored training, process automation, environment security, Teams app development, and migration services around Microsoft 365. Its Power Apps and AI practice adds low-code AI app delivery, AI Builder, Power Apps Copilot, Azure AI, and integrations across Microsoft 365, Power BI, Dataverse, Teams, and SharePoint. For an organisation that wants board-level AI ambition translated into working Microsoft processes, that kind of delivery capability matters. If your company is planning a Microsoft 365 AI rollout, Copilot adoption, or Power Platform automation initiative, TTMS Microsoft 365 services can help turn AI strategy into secure, scalable business execution. FAQ What are the best enterprise AI platforms? For most organisations, the strongest shortlist is Microsoft 365 with Copilot, Google Workspace with Gemini and NotebookLM, OpenAI ChatGPT Enterprise, Salesforce Agentforce, ServiceNow AI Platform and Now Assist, Amazon Q Business, and SAP Business AI with Joule. Each one is strong, but each one solves a different layer of enterprise work. What is the best AI platform for enterprise work in 2026? If the goal is broad company productivity, governance, and cross-functional adoption, Microsoft is the strongest answer in 2026. Google comes next for Workspace-centric companies. If you specifically want a standalone assistant rather than a full workspace stack, OpenAI is the leading option. What should a company avoid when buying an enterprise AI system? Avoid choosing a platform only because the underlying model is fashionable. The better buying criterion is where work already happens, how permissions are handled, how admins control access, how the system connects to company knowledge, and whether it supports real workflows instead of isolated prompting.
ReadLow-code AI Adoption in Pharma: 2026 Guide
Pharmaceutical companies have always faced intense pressure to move faster, spend less, and stay compliant. What’s shifted recently is the nature of the tools available to meet those demands. Low-code AI adoption in pharma is no longer a fringe concept explored by forward-thinking R&D labs. It’s becoming a practical strategy for organizations that need to digitize operations quickly, without building every solution from scratch. This guide is written for pharma IT leaders, digital transformation managers, and compliance officers who want a clear, realistic picture of where low code AI stands in 2026 and how to use it effectively across the life sciences value chain. 1. Why low-code AI is gaining traction in Pharma right now The pharmaceutical sector has historically been slow to adopt new technology, and for good reason. Regulatory obligations, data sensitivity, and patient safety create a conservative environment. But that conservatism carries an increasingly steep price. The global low-code and AI-assisted workflow automation platform market is projected to grow strongly, with Technavio estimating a 32.2% CAGR between 2025 and 2029. For pharma and life sciences organizations, this growth reflects a broader shift toward faster, more governed digitalization of complex workflows. The pressure to digitize isn’t letting up, and the gap between what pharma organizations need to deliver and what their IT teams can realistically build keeps widening. 1.1 The pressure driving faster digital adoption across the life sciences value chain Regulatory demands are intensifying globally. At the same time, operational costs are climbing, and the time between molecule identification and market approval remains under constant scrutiny. Companies face mounting expectations from regulators, patients, and investors to do more with their data, and to do it faster. Traditional software development cycles, often spanning years, simply can’t keep pace. Digital transformation has moved from a strategic priority to an operational necessity. Pharma companies that can’t rapidly digitize clinical data workflows, manufacturing quality processes, or pharmacovigilance functions are accumulating technical debt that compounds every year. 1.2 What low code AI actually means in a pharma context Low code AI refers to platforms that let users build functional, AI-assisted applications through visual interfaces, drag-and-drop tools, and pre-built templates, rather than writing extensive custom code. In a pharma context, this means a quality assurance manager could configure a deviation management workflow, or a clinical operations team could build a data collection form, without waiting months for a development sprint. Two platforms that illustrate this well in enterprise pharma environments are Microsoft Power Apps and Webcon BPS, both of which TTMS implements and supports for regulated industries. Power Apps enables rapid digitization of business processes across departments, while Webcon BPS provides structured workflow automation with a strong focus on compliance and process governance. 1.3 How it differs from traditional AI and full-code development for regulated environments Traditional AI development in pharma typically requires dedicated data science teams, significant infrastructure investment, and long validation cycles. Full-code development offers maximum flexibility but demands specialized developers, extensive documentation, and project timelines that can stretch well beyond what business stakeholders actually need. Low code AI sits between these extremes. It provides enough flexibility to address real business problems, with enough structure to satisfy governance requirements. Crucially, it reduces dependency on highly specialized engineers while still producing auditable, maintainable applications. For regulated environments where every system change requires documented rationale, that balance matters enormously. 2. Key benefits of low code AI adoption in pharma The case for low code AI automation in pharma isn’t theoretical. The concrete operational gains it delivers across the organization, from IT governance to the shop floor, are what make it worth pursuing. 2.1 Speed to deployment: from months to weeks The most immediate advantage is compressed development timelines. Pharma supply chain applications built on low code platforms have demonstrated up to 75% faster development cycles compared to traditional coding approaches, enabling quicker time-to-market for both drugs and supporting applications. In pharmaceutical manufacturing, where process changes need to respond to audit findings or regulatory updates quickly, that speed is operationally significant. This isn’t about cutting corners. It’s about removing the structural inefficiencies that slow traditional development: handoffs between business and technical teams, lengthy requirements documentation cycles, and redundant testing phases. Low code platforms encode many of those quality standards directly into the build environment. 2.2 Empowering citizen developers without sacrificing it governance One of the most practically valuable aspects of low code AI is what it does for non-technical staff. Citizen developers, business users with limited or no formal coding background, can build applications that automate their own workflows. This doesn’t mean IT steps aside; it means IT shifts from writing code to governing platforms, setting standards, and ensuring security. TTMS’s Microsoft Power Apps consulting service is built around exactly this model. By implementing Power Apps within a governed Microsoft Power Platform environment, TTMS enables pharma teams to develop functional apps in their own domain while IT retains control over data connections, compliance configurations, and deployment permissions. Fewer bottlenecks, faster delivery, and IT resources freed for higher-complexity challenges. 2.3 Reducing costs across the pharma value chain Custom software development at enterprise scale is expensive. Beyond developer salaries, costs accumulate in vendor licensing, integration work, project management, and ongoing maintenance. A Forrester TEI low-code study cited by Pega found 598% ROI and $12.5 million in productivity savings over three years for enterprises using Pega’s low-code platform. While this is not pharma-specific, it illustrates the type of financial impact low-code programs may deliver when implemented at scale. For organizations managing dozens of operational systems across manufacturing sites, clinical operations, and regulatory affairs, low code platforms consolidate much of this expense through reusable components, pre-built connectors, and simplified update cycles. 2.4 Maintaining compliance in a low code build environment Compliance is where pharma organizations most commonly hesitate on low code. The concern is legitimate: how do you ensure that applications built by non-developers meet GxP standards, maintain audit trails, and support validation documentation? The answer lies in choosing the right platform and the right implementation partner. TTMS’s Webcon BPS implementation service is specifically designed to address this. As an official Webcon Partner, TTMS deploys Webcon BPS in ways that embed process governance, version control, and audit trail functionality directly into workflow design. Rather than retrofitting compliance onto finished applications, compliance is part of how the application is built from the start. This approach aligns well with the documentation and validation requirements that pharma quality teams manage daily. 3. High-impact use cases across the pharma value chain Low code AI adoption in pharma isn’t limited to a single department or function. Its real value emerges when applied consistently across the value chain, each use case building on the organization’s growing low code maturity. 3.1 Accelerating drug discovery and r&d workflows In early-stage research, scientists spend a significant portion of their time on data entry, status tracking, and reporting. Tasks that add little scientific value but consume hours. Low code platforms can automate these workflows, connecting laboratory information systems with project management tools and enabling AI-assisted data analysis through pre-built connectors to services like Azure AI. TTMS’s background in AI implementation and IT system integration makes this kind of layered solution achievable. A Power Apps-based research tracking application, integrated with existing LIMS and ERP systems, can give R&D teams real-time visibility into experiment status, resource allocation, and milestone progress, without commissioning a full custom development project. 3.2 Improving quality control and compliance in pharmaceutical manufacturing AI in pharmaceutical manufacturing is increasingly focused on anomaly detection, deviation management, and real-time quality monitoring. Low code platforms enable quality teams to build and maintain these workflows themselves, reducing the time between identifying a process gap and deploying a digital solution. Webcon BPS is particularly well-suited here. Its process-centric architecture supports structured deviation workflows, corrective and preventive action tracking, and batch release sign-off processes, all with built-in audit trails that align with GxP documentation expectations. For manufacturers operating across multiple sites, the ability to standardize these processes on a single governed platform is a meaningful operational improvement. 3.3 Streamlining clinical trial data management Clinical trials generate enormous volumes of data from diverse sources: electronic data capture systems, wearables, site management software, and patient-reported outcome tools. Managing this data consistently while maintaining regulatory compliance is a persistent challenge for clinical operations teams. The potential gains here are substantial. Seagen, a biopharmaceutical company, deployed a cloud-native solution to automate clinical trial data publishing and legal/compliance review workflows that previously took up to six months to complete. By integrating the clinicaltrials.gov API directly into their review process, the team reduced approval time from months to minutes. Pfizer’s integration team later recognized the solution as best-in-class, noting that their own equivalent process required six months to approve just three to five trials. It’s a concrete illustration of what targeted automation can achieve in regulated clinical workflows. The same architectural thinking applies when deploying low code AI tools for data aggregation dashboards, automated status reporting, and anomaly-flagging workflows across trial operations. 3.4 Enhancing pharmacovigilance and post-market surveillance Pharmacovigilance requires rapid intake, triage, and reporting of adverse event data. Delays carry both regulatory and reputational risk. Low code AI tools can automate case intake forms, route reports to the correct reviewers, and generate draft narratives using AI assistance, all within a governed workflow that maintains a complete audit trail. Webcon BPS’s workflow architecture maps naturally to the structured, multi-step review processes that pharmacovigilance teams rely on. Combined with TTMS’s experience in IT outsourcing and managed services, organizations can deploy and maintain these solutions without building internal platform expertise from scratch. 3.5 Optimizing supply chain visibility and logistics Pharmaceutical supply chains are complex, tightly regulated, and vulnerable to disruption. Low code AI platforms can surface real-time inventory data, automate reorder triggers, and provide visibility into cold-chain compliance status through dashboards that operations teams can configure and update themselves. Quest Nutra Pharma partnered with Kissflow adoption of a low-code compliance workflow platform is a useful example. By automating quality check tracking, regulatory process updates, and compliance reporting on a single governed platform, the company achieved faster response times when adapting to regulatory changes and reduced non-compliance risk across its operations. Power Apps, connected to enterprise data sources through Power Platform’s broad connector library, offers the same capability for mid-sized pharma companies that need more than a spreadsheet but can’t justify a major ERP customization project. 4. Choosing the right low code ai platform for life sciences Platform selection is where many pharma organizations stall. The market includes dozens of low code tools, and not all of them are suited to the compliance, security, and integration demands of a regulated industry. A structured evaluation process helps narrow the field considerably. 4.1 Core capabilities to evaluate for pharma-specific requirements Any platform evaluation should start with the functional requirements most critical to pharma operations: structured workflow support, role-based access control, document handling, electronic signatures, and AI integration. Beyond features, consider the governance model. Can IT teams set guardrails for what citizen developers can build? Can platform administrators enforce data classification rules? These controls aren’t optional in an environment where data integrity is a regulatory requirement. 4.2 Integration with legacy systems and existing data infrastructure Pharma organizations carry significant legacy system burden. ERP platforms, LIMS, document management systems, and clinical data repositories have often been in place for decades, each with its own data model and integration interface. A low code platform that can’t connect to these systems reliably adds integration risk rather than reducing it. Both Power Apps and Webcon BPS address this challenge directly. Power Apps connects to hundreds of enterprise systems through Power Platform connectors, while Webcon BPS provides REST API support and native integrations with common business systems. TTMS’s broader IT integration expertise means these connections can be designed with the data governance standards that pharma environments require. 4.3 Vendor validation, Audit trails, and 21 CFR Part 11 readiness 21 CFR Part 11 governs the use of electronic records and electronic signatures in FDA-regulated industries. Any low code platform used in a regulated context needs to support the relevant technical controls, including audit trails, access controls, and record integrity measures. Worth noting: platform capability is distinct from validated implementation. A platform designed to support 21 CFR Part 11 compliance still requires a validation protocol, installation qualification, and operational qualification before it can be used in a regulated process. TTMS can supports pharma clients through this validation process, drawing on experience with both Power Apps and Webcon BPS in governance-sensitive environments. This includes helping organizations build the documentation packages, test scripts, and change control procedures that regulators expect. 4.4 Leading platforms used in medtech enterprises and pharma in 2026 Platforms often considered for low-code, workflow automation, or regulated content workflows in pharma and medtech include low code environments include Microsoft Power Platform (encompassing Power Apps, Power Automate, and Power BI), Webcon BPS, Appian, ServiceNow, and Veeva Vault for specific regulatory content workflows. TTMS brings direct implementation experience with both Microsoft Power Apps and Webcon BPS in enterprise environments. The choice between them often comes down to the specific use case: Power Apps excels in broad departmental digitization and user-facing applications, while Webcon BPS is particularly strong for structured, compliance-heavy workflow automation. 5. Common barriers to low code AI adoption in pharma and how to overcome them Even when the business case is strong, adoption rarely happens without friction. The barriers in pharma are distinct from those in other industries, and they require specific strategies to address. 5.1 Regulatory uncertainty and validation concerns The most common hesitation in pharma IT is regulatory. Leaders worry that low code platforms will create compliance gaps, that regulators will scrutinize application builds differently, or that validation costs will negate the speed advantages. These concerns aren’t unfounded, but they’re often overstated. The key distinction is between the platform and the application built on it. A well-governed low code platform, implemented with proper validation protocols, is defensible in an audit. The answer to regulatory uncertainty isn’t to avoid low code; it’s to build robust validation frameworks around its use. TTMS helps pharma clients develop these frameworks as part of its implementation approach, ensuring that speed and compliance reinforce rather than trade off against each other. 5.2 Data quality and interoperability challenges Low code AI only delivers value when the data feeding it is reliable. Many pharma organizations discover their data quality and interoperability challenges are more significant than anticipated once they start digitizing workflows. Master data inconsistencies, siloed systems, and poorly documented data models can slow implementation considerably. Addressing this barrier means treating data governance as a prerequisite, not an afterthought. Before deploying low code AI tools in a new domain, organizations should map their data sources, identify quality issues, and define ownership. TTMS’s experience in IT system integration and business intelligence helps clients build this foundation as part of a broader digital transformation strategy. 5.3 Change management and workforce readiness Technology adoption ultimately depends on people. In pharma, where established processes carry regulatory weight, introducing new tools challenges deeply ingrained working habits. Resistance from quality teams, clinical operations staff, or manufacturing supervisors can stall a well-designed low code program. Effective change management requires more than a training session. It means engaging business stakeholders early in the design process, demonstrating tangible improvements to their day-to-day work, and building internal champions who advocate for the new approach. TTMS’s e-learning capabilities support this by enabling pharma organizations to develop structured training programs that scale adoption across large, distributed teams. 6. What to expect from low code AI in pharma through 2026 and beyond Market forecasts make the growth trajectory concrete. According to Technavio, the global low code AI platform market is projected to grow by USD 32.26 billion at a CAGR of 32.2% through 2029, driven by the democratization of AI, talent scarcity, and generative AI integration across sectors including healthcare. Grand View Research projects the broader low code application development platform market to reach USD 101.68 billion by 2030 at a CAGR of 22.5%, with AI-powered workflow optimization cited as a key growth driver in regulated industries. For pharma specifically, these figures signal a market where low code investment is no longer discretionary. By 2026, organizations that began their low code journeys in 2023 and 2024 will be moving beyond individual applications toward enterprise-wide platforms that govern how low code tools are built, deployed, and maintained. The citizen developer model will mature, with clearer governance frameworks defining what business teams can build independently versus what requires IT involvement. AI capabilities embedded in low code platforms will also deepen. Predictive analytics, natural language processing, and AI-assisted decision support will be available to business users through the same visual interfaces they use to build workflows today. This will raise new questions about model governance, explainability, and regulatory compliance for AI-generated recommendations in clinical and manufacturing contexts. Pharma organizations that build their low code governance structures now will be better positioned to incorporate these capabilities responsibly when the time comes. The relationship between IT and business functions will continue to shift as well. IT becomes a platform enabler rather than the sole application builder, business teams take greater ownership of their digital processes, and the boundary between technology and operations grows more fluid. That’s the direction the industry needs to move. 7. How TTMS can help your organization get the most from low code in pharma Implementing low code AI in a regulated industry isn’t simply a technology project. It’s an operational transformation that requires platform expertise, integration capability, regulatory awareness, and change management discipline. TTMS brings all of these to pharma clients as a single integrated partner. As a recognized Microsoft Power Apps development company, TTMS helps pharmaceutical organizations deploy Power Platform solutions that enable citizen developers while maintaining IT governance. This includes designing the platform architecture, configuring security and data policies, building initial application templates, and training business users to take ownership of their workflows. The result is faster delivery of digital solutions that remain auditable and maintainable. As an official Webcon Partner, TTMS also implements Webcon BPS for pharma clients who need structured, compliance-focused workflow automation. Webcon BPS’s process governance capabilities make it particularly well-suited for quality management, pharmacovigilance, and document control workflows where audit trail integrity and process standardization are non-negotiable. TTMS’s implementation approach incorporates the validation documentation and testing structures that pharma quality teams require. Beyond these two platforms, TTMS’s capabilities extend across the full scope of what a pharma low code program needs to succeed. Its AI implementation expertise enables integration of intelligent automation and predictive analytics into low code workflows. Its IT system integration experience ensures that new applications connect reliably to existing ERP, LIMS, and clinical data systems. Its managed services model means pharma clients can maintain and evolve their low code environments without building a dedicated internal platform team. Its e-learning capabilities allow organizations to develop scalable training programs that bring large, distributed pharma workforces up to speed on new digital tools, accelerating adoption and reducing resistance. If your organization is ready to explore how low code AI can solve real operational challenges, whether in manufacturing quality, clinical operations, supply chain, or pharmacovigilance, TTMS can help you build a practical roadmap and deliver results. Reach out to the TTMS team at ttms.com to start the conversation. FAQ What is low-code AI in the context of pharma? Low-code AI in pharma refers to the use of visual development platforms that incorporate artificial intelligence capabilities, enabling pharma professionals to build and automate applications without extensive programming knowledge. Examples include Microsoft Power Apps for rapid application development and Webcon BPS for structured process automation in regulated workflows. Is low-code AI compliant with pharmaceutical regulations like 21 CFR Part 11? Low-code platforms can be designed and implemented to support 21 CFR Part 11 requirements, including audit trails, electronic signatures, and access controls. Compliance depends on how the platform is configured and validated, though. Organizations must follow appropriate validation protocols regardless of the platform used. What types of Pharma processes benefit most from low-code AI? Quality deviation management, clinical trial data workflows, pharmacovigilance case intake, supply chain visibility, and batch release processes are among the highest-impact use cases. Essentially, any structured, repetitive process that currently relies on manual data entry or email-based approvals is a strong candidate. How long does it take to deploy a low-code AI solution in pharma? Deployment timelines vary by complexity and regulatory scope, but low code platforms routinely reduce development time from months to weeks for standard workflow applications. A validation-ready deviation management workflow, for example, can often be configured and tested within four to six weeks with the right implementation partner. What’s the difference between low-code and no code for pharma? No code platforms are fully visual with no programming required, which limits customization. Low code platforms allow limited scripting alongside visual tools, giving developers more flexibility while still accelerating delivery. For regulated pharma environments, low code’s added flexibility usually makes it the more appropriate choice. How does TTMS support low code AI adoption in pharma? TTMS provides end-to-end low code implementation services, including platform selection, configuration, IT integration, validation support, and training. As both a Microsoft Power Platform partner and an official Webcon Partner, TTMS brings direct platform experience to pharma clients navigating complex digital transformation challenges.
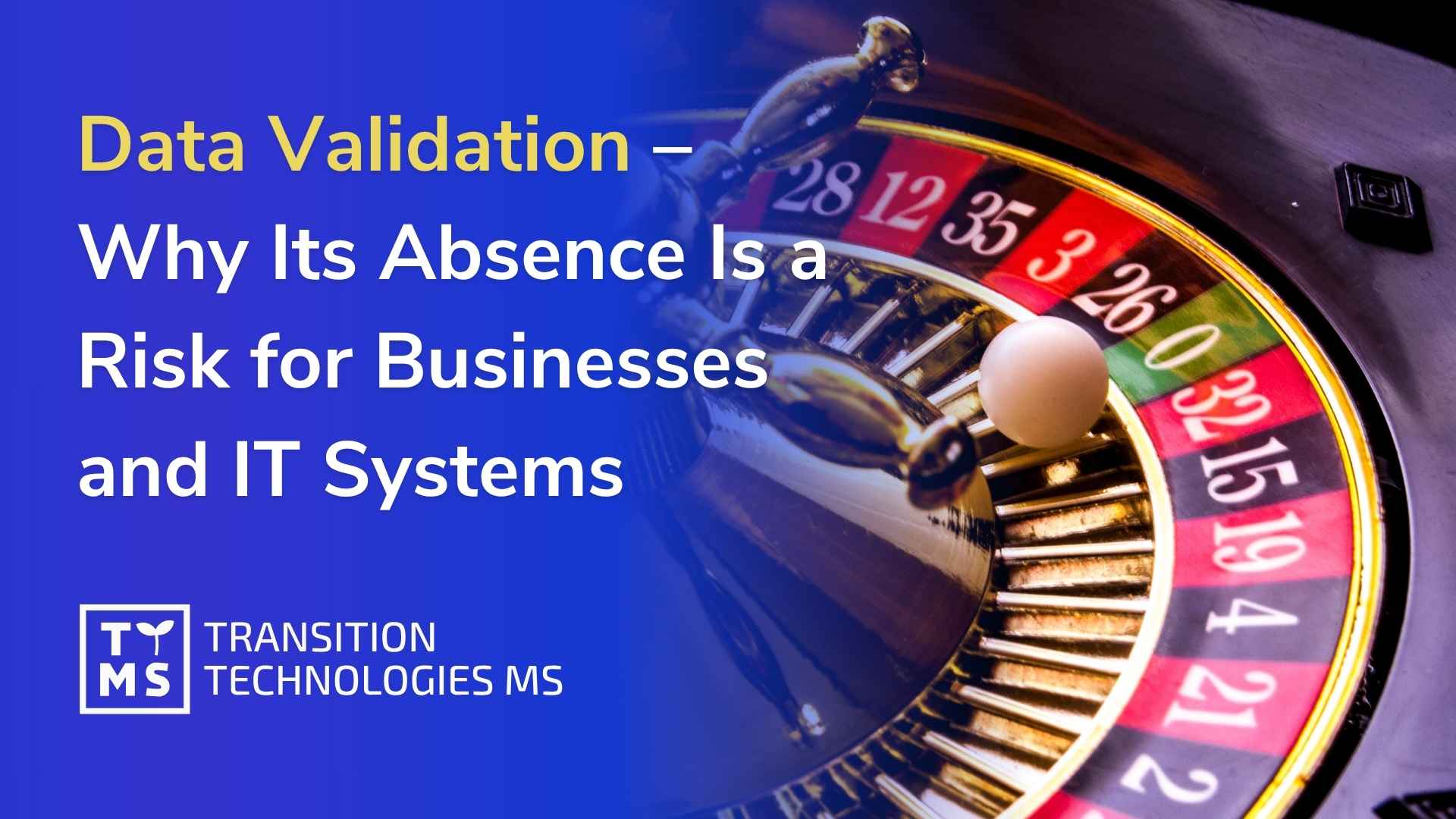
ReadData Validation and Quality: Why Skipping Them Is Risky
In the world of data, a lack of data validation works like a casino roulette. The ball spins around the wheel, and the outcome remains uncertain until the very last moment. Players make decisions, but in the end the result depends on chance. In many organizations, IT system management looks similar. When validation and quality processes are overlooked, system stability stops being a result of control and begins to depend on luck. For a long time, everything may appear to work correctly. The system runs, data is stored, users perform their tasks. The team therefore assumes that since no problems occur, additional validation is not necessary. The issue is that the absence of formal quality processes means there is no certainty that the system operates correctly in every situation. Until an error, audit, or data-related incident occurs, the risk remains invisible. 1. Why organizations overlook validation In many organizations, the decision to implement formal validation processes is postponed. At first glance, systems seem to function properly, projects are delivered, and teams focus on new features and technological development. In such a situation, validation is often seen as an additional step that may slow down the project or increase its cost. The problem, however, is that the lack of structured quality processes rarely causes immediate issues. Risk accumulates gradually, and early symptoms are often ignored or treated as isolated incidents. Over time, organizations begin to notice that the absence of validation makes it harder to control systems, changes, and data. Below are the most common reasons companies delay implementing validation processes, even though in the long run their absence can lead to serious operational and business problems. 1.1 Time pressure in IT projects One of the most common reasons is time pressure. IT projects have tight schedules, and teams want to deliver new features as quickly as possible. In such conditions, tests performed by developers are often considered sufficient quality assurance. Project teams focus primarily on delivering on time, while activities related to documentation, risk analysis, or formal validation are postponed. In practice, this means that many decisions regarding system quality are made under time pressure and without a full analysis of potential consequences. 1.2 False sense of security In many organizations, there is also a belief that if a system operates in a production environment and users do not report major issues, there is no need for additional validation activities. However, this way of thinking leads to a situation where the absence of problems is interpreted as proof that the system works correctly. In reality, the absence of incidents does not always mean the absence of risk. It often simply means that potential errors have not yet surfaced or have not been properly identified. 1.3 Legacy systems and years of modifications Another reason is the belief that if a system has been running for many years, it does not require additional validation. In practice, however, many organizations use systems that have been repeatedly modified, integrated with other tools, or extended with new features. Every change in system architecture, integration with a new tool, or modification of a business process can affect how the entire IT environment operates. Without formal change control, it is difficult to assess whether all components still function predictably and whether new functionalities introduce unexpected dependencies between systems. 1.4 Insufficient awareness of the role of quality An important factor is also the lack of awareness regarding the importance of quality processes. In many technical teams, validation is mainly associated with documentation or additional formalities. In reality, its core role is to ensure that the system operates in accordance with business and technical requirements and that the organization has evidence confirming the correct functioning of key features. 1.5 The documentation myth A common misconception is that quality processes are primarily about documentation. In fact, their main goal is to ensure control over the system and reduce operational risk. A well-designed validation process helps organize system development, increases the transparency of changes, and allows potential issues to be identified earlier, before they affect the organization’s operations. 2. Hidden risks of overlooking quality processes The lack of validation brings a number of risks that are not always visible at first glance. In many organizations, problems become noticeable only when a serious incident, data error, or external audit occurs. Until then, the system may appear to function correctly, giving teams a false sense of security. In reality, however, the absence of quality control leads to a gradual accumulation of risk across the entire IT environment. 2.1 Risk of data integrity loss One of the most serious threats is the risk related to data integrity. If a system has not been properly verified, there is no full certainty that data is processed correctly in every situation. Errors may appear in reports, analyses, or decision-making processes, and their source can be difficult to identify. In practice, this means that an organization may make business decisions based on incomplete or incorrect information. In environments where data is critical to company operations, such situations can lead to serious financial or reputational consequences. 2.2 Lack of change traceability in the system Another problem is the lack of transparency in system changes. Without proper documentation and change control, the organization does not have clear information about when and why specific modifications were introduced. In practice, this means a lack of full traceability of actions within the system. When a problem arises, technical teams often spend many hours or days trying to determine which change could have affected system behavior. The lack of a clear change history makes incident root cause analysis more difficult and significantly extends resolution time. 2.3 System instability and unpredictable errors Risk also arises in the context of system stability. Even a small change can affect other elements of the IT environment. Integrations with other systems, reporting mechanisms, or automated processes may function correctly for a long time, only to fail after a seemingly minor modification. Such situations are particularly dangerous in complex technological environments, where one system is connected to many other tools. The lack of an appropriate testing process and risk assessment means that the organization does not have full control over the impact of changes introduced into the production environment. 2.4 Increasing operational and technical costs Low-quality IT processes often also lead to increased operational costs. Technical teams spend more time resolving issues, analyzing incidents, and manually correcting errors in data or systems. In the long run, the absence of structured quality processes makes system development increasingly difficult. Each subsequent change carries greater risk, and project teams become more conservative, fearing unpredictable consequences of modifications. As a result, the pace of technological development within the organization slows down, and system maintenance becomes increasingly expensive. 3. When the lack of validation starts to have a real cost In many organizations, issues related to the lack of validation remain invisible for a long time. Systems operate, business processes are carried out, and technical teams focus on day-to-day tasks and further technological development. Over time, however, the first warning signs begin to appear: difficulties in analyzing errors, a lack of a clear change history in the system, or an increasing number of incidents whose root causes are hard to determine. It is at this point that organizations realize that the absence of structured quality processes is not merely a formal issue, but a real operational and business problem. In such moments, organizations begin to see that validation is not an additional burden, but a tool that makes it possible to regain control over systems, data, and IT processes. 3.1 The moment when risk stops being theoretical In many organizations, the decision to implement formal validation processes arises only when risk takes on a very tangible business dimension. For a long time, the lack of validation may not cause visible problems. The system works, processes are carried out, and teams focus on further technological development. 3.2 Audits and partner assessments The situation changes, however, during an audit, a shift in regulatory requirements, or an assessment by business partners. Increasingly, contractors expect confirmation that IT systems are managed in a controlled manner and in accordance with established quality standards, which may support compliance with regulatory requirements. 3.3 Risk of losing partners and trust In such situations, the lack of validation can lead to a loss of trust among business partners. An organization that is unable to demonstrate that its systems are properly tested and monitored may be considered too risky as a technology partner. 3.4 Financial penalties and regulatory consequences In some industries, the consequences may be even more severe. Non-compliance with regulatory requirements can result in financial penalties, the need to implement costly corrective actions, or the suspension of certain operational processes. 3.5 Validation as protection of business relationships This is why more and more companies are beginning to treat validation not as an additional obligation, but as a means of protecting business relationships and organizational stability. Quality processes are no longer seen solely as a formal requirement. They become a tool that helps maintain the trust of clients, partners, and supervisory institutions, while also improving preparedness for regulatory requirements. 4. How validation transforms chance into control Validation introduces structure and predictability into IT system management. Instead of relying on assumptions, the organization relies on evidence confirming the correct operation of the system. The validation process includes structured functional testing, documentation of requirements, and control of changes within the system environment. This makes it possible to confirm that the system operates in line with business and technical assumptions. An important element is also a risk-based approach. Not all systems require the same level of validation. In practice, this means focusing on areas that have the greatest impact on data, business processes, or regulatory compliance. 5. Quality processes as part of risk management In many organizations, quality processes are perceived as something that slows down technology projects. In reality, their role is entirely different. Their purpose is not to create documentation for its own sake, but to ensure that systems operate in a stable and predictable manner. Companies that treat validation as part of risk management gain greater control over their systems. They are also better prepared for audits and can more easily identify potential issues before they affect business operations. Without validation, every change in the system resembles another spin of the roulette wheel. The outcome may be favorable, but it may also bring unexpected consequences. Implementing quality processes makes it possible to replace chance with control and ensures that IT systems become a stable foundation for organizational operations. 6. Why trust the Quality team at TTMS Effective validation of IT systems requires a combination of technological expertise, knowledge of business processes, and experience in quality and regulatory compliance. This is exactly the approach taken by the Quality team at TTMS. TTMS experts support organizations in building structured validation processes that ensure data security and system stability. Thanks to their experience working with business-critical systems, they help design solutions that meet quality requirements and can support organizations in meeting regulatory requirements, while also enabling efficient technological development. The TTMS approach is based on risk analysis, transparent documentation, and close collaboration with both technology and business teams. As a result, the validation process becomes a factor that supports system development rather than a barrier to innovation. Contact us now! 7. FAQ What is IT system validation? IT system validation is a process that confirms a system operates in accordance with defined requirements and fulfills its intended purpose in a business environment. It includes functionality testing, risk analysis, and documentation of results. Through validation, an organization has evidence that the system operates correctly and can be safely used in operational processes. Why skipping validation poses a risk to an organization? Skipping validation means there is no certainty that the system operates correctly. Issues may arise in data processing, reporting, or integration with other systems. In the event of an audit or an incident, the organization may have difficulty proving that the system was properly tested and controlled. Does every IT system require validation? Not every system requires the same level of validation. In practice, a risk-based approach is applied. Systems that impact critical data, regulated processes, or business decisions require more detailed verification. In other cases, the scope of validation may be limited. What elements does the validation process include? The validation process includes, among others, requirements analysis, preparation of a validation plan, functionality testing, documentation of results, and control of system changes. An important element is the traceability of requirements and tests, which makes it possible to track whether all functionalities have been properly verified. How can an organization start building a validation process? The first step is identifying systems that have the greatest impact on business operations and data security. Next, it is advisable to conduct a risk analysis and define the scope of necessary validation activities. In many cases, support from teams experienced in designing quality processes and IT system validation is helpful.
ReadDigital Transformation in 2026: What It Really Means for Business
Most companies today are already “digital.” They use cloud tools, collect data, and experiment with AI. Yet very few see real financial impact. This is the paradox of 2026: technology adoption is widespread, but business transformation is not. Digital transformation no longer means implementing new tools. It means fundamentally changing how a company operates, makes decisions, and delivers value using technology. 1. What digital transformation really means in 2026 In 2026, digital transformation is no longer about simply digitizing processes, migrating systems to the cloud, or implementing another software platform. Most organizations have already completed those first-generation digital initiatives years ago. Today, transformation means something much deeper: redesigning how the entire business operates in an environment shaped by AI, automation, real-time data, and rapidly changing customer expectations. It involves rethinking: how decisions are made across the organization, how processes are structured and optimized, how data flows between teams and systems, how employees interact with technology in their daily work, how companies respond to market changes in real time. Technology itself is no longer the competitive advantage. Access to cloud infrastructure, AI models, and enterprise software has become widely available. What differentiates companies in 2026 is their ability to integrate these technologies into the core of their operations and turn them into measurable business outcomes. That is why successful transformation programs focus less on tools and more on workflows, governance, accountability, and execution. AI alone does not create value if it is layered on top of inefficient processes. Real impact appears when organizations redesign workflows around automation and data-driven decision-making. For example, many companies initially used AI as a support tool for employees. Today, leading organizations are redesigning entire operational models around AI-assisted workflows. Customer service teams are changing how they handle inquiries, finance departments are automating analysis and reporting, and operations teams are using predictive systems to optimize planning and reduce downtime. The same shift is happening at the leadership level. Executives increasingly expect real-time visibility into operations, faster access to insights, and the ability to make decisions based on live business data rather than static reports prepared days or weeks earlier. Digital transformation also requires cultural and organizational change. Teams must learn to operate differently, managers need new performance metrics, and companies must establish governance frameworks for AI, cybersecurity, compliance, and data quality. In practice, this means that digital transformation in 2026 is no longer an IT initiative. It is a business strategy supported by technology. Companies that succeed are not those that simply “use AI.” They are the ones that redesign their business around it. 2. Why 2026 is a turning point Several forces have converged to make transformation unavoidable. 2.1 AI is becoming operational, not experimental AI is no longer limited to pilots and proofs of concept. It is being embedded into customer service, operations, finance, and decision-making processes. The key shift is from automation of tasks to automation of decisions. 2.2 Data has become a strategic asset Organizations are moving away from fragmented data silos toward integrated data ecosystems that enable real-time insights and AI-driven workflows. 2.3 Regulation is shaping digital strategy New regulations around AI, cybersecurity, and data governance are forcing companies to treat digital transformation as a structured, compliant program rather than a series of experiments. 2.4 Efficiency pressure is higher than ever Rising costs, talent shortages, and market volatility are pushing companies to improve productivity without increasing headcount. Digital transformation is now one of the few scalable ways to achieve that. 3. Where companies are already seeing value The most successful transformations are not theoretical. They focus on specific, measurable outcomes. Across industries, companies are using AI and automation to: reduce customer service costs while improving response times, accelerate decision-making in operations and logistics, improve quality and reduce defects in manufacturing, increase productivity in knowledge-based roles, optimize resource usage and operational efficiency. The common denominator is clear: measurable impact on cost, speed, and quality. 4. What digital transformation is not Many initiatives fail because they are based on outdated assumptions. Digital transformation is not: implementing a new system, moving infrastructure to the cloud, deploying AI without changing processes, running isolated innovation projects. Without process redesign and clear business ownership, these initiatives rarely deliver value. 5. How to approach transformation in practice Successful transformation programs follow a structured approach focused on business outcomes. 5.1 Start with business objectives Define what the transformation is expected to improve before choosing any technology. The objective should be specific enough to guide decisions, budgets, and priorities. Examples of clear objectives include reducing invoice processing time, lowering customer service costs, shortening reporting cycles, improving forecast accuracy, increasing sales team productivity, or reducing production downtime. Each objective should be linked to a measurable KPI. Without this, it is difficult to prove whether the initiative created business value or only introduced another system into the organization. 5.2 Identify high-impact use cases Once business objectives are clear, the next step is to identify use cases with the strongest potential impact. These are usually processes that are repetitive, data-heavy, slow, expensive, or dependent on manual decisions. Good candidates include customer support automation, document processing, financial reporting, demand forecasting, predictive maintenance, quality control, internal knowledge search, and workflow automation. The best use cases combine three elements: clear business value, available data, and realistic implementation complexity. A use case may be attractive on paper, but if the required data is missing or the process depends on too many exceptions, it may not be the right first project. 5.3 Prepare data and architecture Before building solutions, companies need to assess whether their data and systems are ready to support transformation at scale. Poor data quality, disconnected systems, and unclear ownership can block even well-designed initiatives. This stage should include checking where key data is stored, who owns it, how reliable it is, how often it is updated, and whether it can be safely accessed by new applications, analytics tools, or AI systems. Architecture also matters. Solutions should not be designed as isolated pilots. They need to integrate with existing systems, follow security requirements, support future scaling, and allow monitoring after deployment. 5.4 Build and test quickly Transformation should move from assumptions to validation as quickly as possible. Instead of designing a large program for many months, companies should build a minimum viable solution and test it in a real business environment. The goal is not to create a perfect product immediately. The goal is to verify whether the solution improves the target process, whether users can work with it, and whether the expected business value is realistic. A good pilot should have a defined scope, a small group of users, baseline metrics, success criteria, and a clear decision point: scale, improve, or stop. 5.5 Scale what works A successful pilot is not the end of transformation. It is only proof that a solution can work in controlled conditions. The real value appears when the solution is adopted across teams, departments, or business units. Scaling requires more than copying the same tool into another area. Companies need standardized processes, integration with core systems, user training, support models, governance, and clear ownership after rollout. This is also the moment to check whether the solution remains reliable at higher volume, whether costs stay under control, and whether business KPIs continue to improve outside the initial pilot group. 5.6 Manage change actively Digital transformation changes how people work, not only which tools they use. Employees may need to follow new workflows, trust automated recommendations, use new dashboards, or shift from manual execution to supervision and exception handling. Change management should start before deployment. Teams need to understand why the change is happening, how it affects their daily work, what benefits it brings, and what skills they need to build. Leadership alignment is equally important. If managers continue to measure performance in the old way, employees will often return to old processes. New tools must be supported by updated responsibilities, KPIs, training, and communication. 6. Build, buy, or outsource? One of the key strategic decisions in digital transformation is how to deliver it. There is no universal answer, but in practice: building internally gives control but requires significant investment and time, buying ready-made solutions accelerates implementation but limits flexibility, outsourcing enables access to expertise and faster execution. Most companies adopt a hybrid approach, combining internal ownership with external expertise to accelerate delivery and reduce risk. 7. How to measure success of digital transformation? Transformation should always be tied to measurable outcomes. Key metrics typically include: cost reduction, process cycle time, productivity per employee, quality and error rates, time-to-market. Without clear KPIs, even technically successful projects may fail to deliver business value. 8. Final thoughts Digital transformation in 2026 is no longer measured by the number of tools a company implements. It is measured by operational impact. Organizations investing in AI, automation, cloud infrastructure, and data platforms expect measurable improvements in efficiency, speed, and profitability. If transformation initiatives do not reduce costs, improve decision-making, accelerate delivery, or increase productivity, they quickly lose executive support. This is why the most successful companies approach transformation as a business program with clearly defined KPIs, ownership, and timelines rather than a collection of isolated IT projects. In practice, the gap between leaders and lagging organizations is becoming increasingly visible. Companies that move early are: automating repetitive operational work, reducing dependency on manual processes, improving customer response times, using AI to support decision-making, scaling operations without proportional headcount growth. At the same time, organizations that delay transformation are facing rising operational costs, slower execution, fragmented systems, and growing pressure from competitors that operate more efficiently. One of the biggest changes in 2026 is that access to technology is no longer the differentiator. AI tools, cloud services, and enterprise platforms are widely available. The real challenge is execution. Many companies still struggle with: poor data quality, legacy systems that cannot scale, isolated AI pilots with no business impact, lack of internal expertise, unclear ownership of transformation initiatives. As a result, the companies generating the highest value are not necessarily the ones spending the most on technology. They are the ones that can connect strategy, processes, data, and execution into one scalable operating model. That is what digital transformation really means in 2026. It is not a technology trend. It is an operational and strategic capability that directly affects competitiveness, resilience, and long-term growth. Planning a digital transformation or AI initiative? Explore how experienced engineering teams can support faster delivery and lower risk: https://ttms.com/outsourcing/ FAQ How long does a typical digital transformation project take? The timeline depends on the scale of the organization, the complexity of existing systems, and the scope of the transformation. Smaller initiatives such as workflow automation or AI-powered reporting can deliver measurable results within a few months, while enterprise-wide transformation programs often evolve over several years. Most successful companies approach transformation incrementally rather than attempting a complete overhaul at once. What is the biggest obstacle to successful digital transformation? In many organizations, the biggest challenge is not technology but operational alignment. Companies often struggle with fragmented systems, unclear ownership, resistance to change, or lack of coordination between business and IT teams. Even strong technical solutions can fail if the organization is not prepared to adapt processes, responsibilities, and decision-making models around them. Can mid-sized companies benefit from AI-driven transformation? Yes. In fact, mid-sized companies often move faster than large enterprises because they have fewer legacy systems and shorter decision-making chains. AI and automation are no longer limited to corporations with massive budgets. Many modern cloud-based tools allow mid-sized organizations to improve efficiency, automate repetitive work, and gain better operational visibility without building complex infrastructure from scratch.
ReadPharma Quality Control – Best Practices in 2026
Patient safety hinges on one critical foundation: pharmaceutical quality control. As drug manufacturing grows more complex and regulatory scrutiny intensifies, companies must balance precision with efficiency while navigating a landscape transformed by digital innovation. Quality control now demands a strategic blend of traditional rigor and cutting-edge technology, creating a framework where every test, every data point, and every process decision directly impacts the medications that reach patients worldwide. The financial stakes underscore this reality. Large-scale recalls exceed $100 million per event, while pharmaceutical companies collectively spend $50 billion annually on compliance despite $1.1 billion in penalties over the past five years. More telling, the FDA issued 105 warning letters for quality issues in fiscal year 2024, representing the highest count in five years and a 21% increase from the previous year. At the same time, pharmaceutical companies face increasing pressure to modernize their quality control environments with validated digital systems. The integration of laboratory platforms, manufacturing systems, and quality management tools is becoming essential not only for efficiency, but also for maintaining compliance with evolving regulatory expectations. 1. Understanding Pharmaceutical Quality Control in 2026 1.1 What Pharma Quality Control Encompasses Today Pharmaceutical quality control represents the systematic examination and testing of drug products to ensure they consistently meet predefined specifications for safety, efficacy, and purity. This discipline validates every component entering production, monitors critical parameters during manufacturing, and confirms final products meet regulatory standards before reaching patients. Quality control operates as both gatekeeper and diagnostic system. It verifies raw material identity and purity, tracks manufacturing processes to detect deviations before they compromise product integrity, and validates finished products against specifications covering identity, potency, dissolution, and contamination limits. This multi-layered approach catches potential issues early and prevents defective products from entering the supply chain. The scope integrates environmental monitoring, equipment qualification, and cleaning validation alongside traditional product testing. Quality control analysts work within a framework that demands meticulous documentation, validated analytical methods, and adherence to protocols that withstand regulatory scrutiny. 1.2 The Evolution: How QC Has Changed Leading Into 2026 Traditional approaches relied heavily on end-product testing, where manufacturers identified problems only after investing significant time and resources into production. This model created bottlenecks, wasted materials, and delayed market access when issues surfaced late in the manufacturing cycle. Modern quality control embraces proactive methodology centered on continuous monitoring and data-driven decision-making. Advanced analytics now enable real-time visibility into process parameters, allowing teams to identify trends and address potential deviations before they affect product quality. This evolution recognizes that quality cannot be tested into products but must be built into processes from inception through final packaging. Risk-based thinking has revolutionized how pharmaceutical companies allocate quality control resources. Rather than applying uniform testing intensity across all products and processes, organizations now prioritize efforts based on patient risk, process complexity, and historical performance data. The integration of Quality by Design principles further reinforces this shift, encouraging manufacturers to understand and control process variables that directly impact product attributes. This shift toward proactive quality control is tightly linked with the adoption of digital systems such as Laboratory Information Management Systems (LIMS), Manufacturing Execution Systems (MES), and Quality Management Systems (QMS). Ensuring that these systems are properly validated and integrated has become a critical requirement for maintaining both operational efficiency and regulatory compliance. 2. Core Quality Control Testing and Processes in Pharmaceuticals 2.1 Raw Material Testing and Incoming Quality Control Raw material testing forms the first defense against quality problems. Every ingredient arriving at production facilities undergoes rigorous identity verification, often using spectroscopic methods that create unique molecular fingerprints. These tests confirm suppliers delivered the correct material, preventing mix-ups that could compromise entire batches. Beyond identity confirmation, incoming quality control assesses material purity through quantitative analysis. Companies test for specified impurities, residual solvents, and heavy metals that might affect product safety or stability. This screening catches substandard materials before they enter production, protecting both product quality and patient safety while avoiding costly downstream failures. Supplier qualification and performance monitoring complement physical testing, creating a comprehensive incoming quality control strategy. Leading manufacturers maintain approved vendor lists based on audit results, quality history, and certification status. 2.2 In-Process Quality Control During Manufacturing In-process quality control monitors critical parameters throughout production, catching deviations when corrective action can still salvage batches. Manufacturing teams collect samples at predetermined intervals, testing attributes like blend uniformity, dissolution rates, and coating thickness to validate that processes remain within established control limits. Real-time monitoring systems have transformed in-process quality control from periodic sampling to continuous surveillance. Process analytical technology instruments measure critical quality attributes without removing samples, providing immediate feedback on process performance. This approach enables rapid adjustments, reduces waste, and enhances process understanding. Environmental monitoring during manufacturing adds another layer of quality assurance, particularly for sterile products. Regular testing of air quality, surface cleanliness, and personnel hygiene ensures production environments meet stringent standards, preventing contamination that could compromise product safety. 2.3 Finished Product Quality Control and Release Testing Finished product testing represents the final verification that manufactured batches meet all quality specifications before release. Comprehensive testing panels evaluate identity, potency, purity, and physical characteristics like appearance, dissolution, and uniformity. Each test must fall within predetermined acceptance criteria established during product development and validated to ensure reliable results. Pharmaceutical quality control testing follows validated analytical methods that demonstrate accuracy, precision, and specificity. Laboratories maintain extensive documentation proving their methods reliably measure intended attributes without interference from other components. Release testing timelines directly impact manufacturing efficiency and market supply. Advanced analytical instrumentation and streamlined laboratory workflows help reduce turnaround times while maintaining rigorous standards. Some manufacturers implement real-time release testing protocols that use in-process data to certify batches immediately upon completion, though this approach requires substantial validation and regulatory approval. 2.4 Stability Testing and Ongoing Product Monitoring Stability testing assesses how pharmaceutical products maintain quality attributes over time under various environmental conditions. This long-term monitoring program confirms that drugs remain safe and effective throughout their intended shelf life, supporting expiration date assignments and storage recommendations. Accelerated stability studies complement real-time stability programs, using elevated stress conditions to predict long-term behavior more quickly. These studies help identify potential degradation pathways and inform formulation improvements during development. For marketed products, stability monitoring continues throughout the product lifecycle. Trending analysis of stability results can reveal emerging issues before they impact product quality, enabling proactive interventions. This ongoing surveillance demonstrates a manufacturer’s commitment to quality beyond initial product approval. 3. 2026 Best Practices for Pharmaceutical Quality Control 3.1 Risk-Based Quality Control Approaches Risk-based quality control prioritizes resources and attention on areas with the greatest potential impact on product quality and patient safety. This methodology evaluates process complexity, criticality to patient outcomes, and historical performance data to determine appropriate testing intensity and frequency. A sterile-injectable drug manufacturer demonstrated this approach’s effectiveness by implementing AI-driven risk management in their quality management system. According to a BioProcess International analysis and illustrative case study, AI-assisted change-control workflows reduced impact assessment time from 2-4 weeks to approximately one week. According to a BioProcess International illustrative case study, AI-assisted change-control workflows reduced impact assessment time from 2-4 weeks to approximately one week. The example suggests that AI may help accelerate documentation review, change assessment, and audit preparation, provided that the system is validated and governed appropriately. Implementing risk assessment tools enables pharmaceutical companies to make objective decisions about quality control strategies. Failure mode and effects analysis systematically identifies potential failure points and ranks them by severity, occurrence likelihood, and detection difficulty. This structured approach ensures critical risks receive adequate attention while avoiding unnecessary testing that consumes resources without proportional quality benefit. 3.2 Real-Time Release Testing (RTRT) Implementation Real-time release testing represents an advanced quality control strategy where manufacturers certify products using process data instead of traditional end-product testing. This approach uses continuous monitoring and process analytical technology to demonstrate that manufacturing remained within validated control limits that ensure quality. Digital workflows, automation, and real-time monitoring can shorten deviation investigation and closure timelines by improving data availability, traceability, and root-cause analysis. However, the scale of improvement depends on process maturity, validation scope, and system integration. Implementing RTRT requires substantial upfront investment in process understanding, control strategy development, and validation. Companies must demonstrate that monitored process parameters reliably predict finished product attributes and that control systems prevent deviations that could compromise quality. Regulatory authorities scrutinize RTRT proposals carefully, requiring comprehensive evidence that this alternative approach provides equivalent or better quality assurance. The benefits extend beyond reduced testing time. Continuous process monitoring enhances process understanding and enables more responsive manufacturing operations. When deviations occur, process data provides detailed insights into root causes, facilitating faster investigation and corrective action. 3.3 Integrated Quality by Design (QbD) Principles Quality by Design principles shift quality control focus from testing finished products to designing robust processes that consistently produce quality results. This proactive approach, outlined in ICH Q8-Q14 guidelines, identifies critical quality attributes early in development, then designs processes and control strategies that reliably deliver products meeting those targets. Design space concepts allow manufacturers to define operating ranges where processes consistently meet quality standards. Within validated design spaces, companies can adjust parameters without requiring regulatory approval, providing operational flexibility while maintaining quality assurance. ICH Q12, finalized in January 2020, further supports this through lifecycle management tools like Post-Approval Change Protocols. Integrating QbD principles transforms quality control from reactive testing to proactive assurance. When manufacturers understand how process variables affect product attributes, they can implement control strategies that prevent quality issues rather than detecting them after they occur. 3.5 Data Integrity and Electronic Record Management Data integrity forms the foundation of trustworthy pharmaceutical quality control. Documentation issues, incomplete records, and data integrity weaknesses remain recurring themes in regulatory observations and warning letters. In digital quality environments, this makes audit trails, access controls, traceability, and user accountability critical components of compliance. Electronic systems managing quality control data must implement controls preventing unauthorized modifications while maintaining complete audit trails documenting all data handling activities. Regulatory frameworks such as 21 CFR Part 11 and EU Annex 11 require that electronic records and signatures are secure, traceable, and attributable. This makes computer systems validation a fundamental component of modern quality control environments, ensuring that digital systems consistently perform as intended and maintain data integrity throughout their lifecycle. FDA’s Computer Software Assurance (CSA) guidance supports a risk-based approach to software assurance for production and quality system software, with greater focus on intended use, process risk, and patient safety. Quality systems require robust electronic record management practices that withstand regulatory scrutiny. Pharmaceutical companies implement access controls, electronic signatures, and automated backups that ensure data security and availability. The transition from paper-based to electronic quality control systems introduces new challenges alongside efficiency gains. Organizations must train personnel on data integrity principles and maintain vigilance against shortcut behaviors that compromise record reliability. Strong quality culture combined with technical controls creates an environment where data integrity becomes second nature. 4. Common Gaps in Modern Pharmaceutical Quality Control Despite significant advancements in pharmaceutical manufacturing, many organizations still struggle with fundamental gaps in their quality control operations. One of the most common challenges is the lack of integration between systems, where laboratory, manufacturing, and quality data are stored in disconnected platforms. This fragmentation limits visibility and slows down decision-making. Manual processes remain another critical issue. Paper-based documentation, manual data entry, and non-standardized workflows increase the risk of human error and create inefficiencies that impact both compliance and operational performance. In addition, many companies face difficulties maintaining validated system environments. As digital tools evolve, ensuring that all systems remain compliant with regulatory requirements becomes increasingly complex, particularly when multiple systems interact across the organization. Finally, audit readiness is often reactive rather than proactive. Organizations may struggle to quickly provide complete, accurate, and traceable documentation during inspections, increasing the risk of findings and delays. 4.1 The Role of Validated Digital Systems in Quality Control Modern pharmaceutical quality control is heavily dependent on digital systems that support data collection, analysis, and reporting. Platforms such as Laboratory Information Management Systems (LIMS), Quality Management Systems (QMS), and Manufacturing Execution Systems (MES) form the backbone of quality operations. However, implementing these systems is only part of the challenge. Regulatory expectations require that all critical systems are validated to ensure they operate consistently, securely, and in accordance with intended use. Computer systems validation (CSV) plays a key role in achieving this, covering the entire lifecycle from system design and implementation to maintenance and change management. Validated systems enable reliable data integrity, support audit trails, and ensure traceability across processes. They also provide the foundation for integrating advanced technologies such as automation and AI, allowing organizations to modernize their quality control operations without compromising compliance. 4.2 Qualification, Validation, and Continuous Compliance Qualification and validation are essential components of pharmaceutical quality control, ensuring that equipment, systems, and processes consistently perform as intended. This includes installation qualification (IQ), operational qualification (OQ), and performance qualification (PQ), which together confirm that systems are properly installed, operate correctly, and deliver expected results under real conditions. Beyond initial validation, organizations must maintain a state of continuous compliance. Changes to systems, processes, or regulations require ongoing assessment and, where necessary, revalidation. This lifecycle approach ensures that quality control environments remain compliant over time, even as technologies and operational requirements evolve. A structured validation strategy not only supports regulatory compliance but also improves operational reliability, reduces risks, and enhances confidence in quality data. 4.3 Preparing for Audits and Regulatory Inspections Regulatory inspections are a critical aspect of pharmaceutical quality control, requiring organizations to demonstrate full control over their processes, data, and systems. Audit readiness is therefore not a one-time activity, but an ongoing process that involves maintaining up-to-date documentation, ensuring data traceability, and continuously monitoring compliance. Effective preparation includes regular internal audits, gap assessments, and documentation reviews. These activities help identify potential issues before they are exposed during official inspections, reducing the risk of findings and operational disruptions. Organizations that adopt a proactive approach to audits are better positioned to respond quickly to regulatory inquiries, demonstrate compliance, and maintain trust with regulatory authorities. 4.4 Cybersecurity in Pharmaceutical Quality Systems As pharmaceutical quality control becomes increasingly digital, cybersecurity has emerged as a critical component of compliance and risk management. Quality systems handle sensitive data, including product specifications, test results, and manufacturing records, making them a potential target for cyber threats. Ensuring the security of these systems involves implementing robust access controls, data encryption, network protection, and continuous monitoring. Cybersecurity measures must also align with regulatory expectations, ensuring that data remains accurate, protected, and accessible only to authorized users. Integrating cybersecurity into quality control operations helps protect data integrity, prevent unauthorized access, and ensure business continuity in the face of evolving digital risks. 5. Modern Technologies Transforming Pharma Quality Control 5.1 AI and Machine Learning in Quality Testing Artificial intelligence and machine learning algorithms are revolutionizing pharmaceutical quality control by identifying patterns and hidden connections that escape human detection. These systems analyze vast datasets from multiple sources, detecting subtle correlations between process parameters and quality outcomes. Agilent’s Singapore manufacturing facility implemented AI-driven visual inspections, predictive testing, robotics, and digital twin technologies as part of its Industry 4.0 transformation. According to World Economic Forum and Agilent materials, the initiative improved productivity, reduced cycle times, and lowered quality-related manufacturing costs. Similarly, a sterile manufacturing company implementing AI-driven cleanroom environmental monitoring achieved a 15% reduction in environmental deviations and a 25% reduction in contamination-related corrective and preventive actions. Full disclosure: TTMS supports pharmaceutical companies with AI implementation and technology enablement. When evaluating AI solutions for quality control, companies should assess validation requirements, data quality dependencies, and implementation complexity. While AI shows promise, implementation challenges include extensive validation requirements, the need for high-quality training data, and specialized expertise. These systems require careful validation and ongoing performance monitoring to ensure algorithms function reliably across different scenarios. However, implementing AI in regulated environments introduces additional challenges, including model validation, data governance, and integration with existing validated systems. Organizations must ensure that AI-driven processes remain transparent, auditable, and compliant with regulatory expectations. 5.2 Automated Inspection Systems and Robotics Automated inspection systems bring unprecedented consistency and speed to pharmaceutical quality control operations. Robotic platforms perform repetitive tasks like sample preparation and instrument loading with precision that eliminates human variability. High-speed vision systems inspect millions of units for defects, detecting anomalies in appearance, labeling, or packaging that manual inspection might miss. These automated systems integrate seamlessly with laboratory information management systems, creating paperless workflows that enhance data integrity and traceability. Robotics reduce manual handling errors while freeing quality control analysts to focus on complex problem-solving and data interpretation rather than routine mechanical tasks. Process automation offerings from specialized providers help pharmaceutical companies implement and maintain these sophisticated systems. The transition to automated quality control requires careful planning, from equipment selection through personnel training and validation. When executed thoughtfully, automation transforms quality control operations from labor-intensive bottlenecks into streamlined, efficient processes. To fully realize the benefits of automation, inspection systems must be seamlessly integrated with existing laboratory and enterprise platforms, such as LIMS, ERP, and QMS. This integration ensures consistent data flow, traceability, and alignment with broader quality management processes. 5.3 Advanced Analytical Methods and Instrumentation Next-generation analytical instruments provide pharmaceutical quality control laboratories with unprecedented measurement capabilities. Mass spectrometry systems detect and quantify impurities at parts-per-billion levels, ensuring product purity meets increasingly stringent standards. Advanced chromatography techniques separate and measure multiple compounds simultaneously, accelerating testing while improving data quality. Portable and miniaturized analytical devices are bringing quality control testing closer to manufacturing operations. Handheld spectrometers enable rapid raw material identification at receiving docks, while benchtop instruments in production areas support in-process testing without sample transport to central laboratories. The sophistication of modern analytical instrumentation demands corresponding expertise in method development, validation, and troubleshooting. Current analytical procedure lifecycle approaches increasingly emphasize ongoing monitoring and performance verification rather than treating method validation as a one-time activity. This combination of advanced technology and skilled personnel creates quality control operations capable of meeting today’s rigorous standards. 6. Regulatory Compliance and Standards in Pharma Quality Control 6.1 Global Regulatory Framework Overview (FDA, EMA, ICH) Pharmaceutical quality control operates within a complex global regulatory landscape where agencies like the FDA, EMA, and ICH establish standards protecting patient safety. The FDA governs pharmaceutical manufacturing and testing requirements in the United States through comprehensive regulations covering everything from laboratory practices to documentation standards. European Medicines Agency guidelines apply similar rigor within European Union markets. International Council for Harmonisation guidelines promote consistency across major pharmaceutical markets. ICH documents covering analytical validation, stability testing, and impurity qualification provide science-based frameworks that regulatory authorities worldwide have adopted. The ICH Q10 Pharmaceutical Quality System, updated with ICH Q9(R1) in 2023 and a minor correction in 2025, emphasizes lifecycle management, CAPA, monitoring, and continual improvement. ICH Q9(R1), revised in January 2023 and corrected in 2025, clarifies risk management principles for digitalization, supporting data quality in inspections. This harmonization simplifies compliance for global pharmaceutical companies while ensuring consistent quality regardless of manufacturing location. In practice, maintaining compliance requires continuous audit readiness, structured documentation, and the ability to demonstrate control over both processes and supporting systems. Organizations increasingly rely on external expertise to assess gaps and prepare for regulatory inspections. 6.2 cGMP Compliance Requirements for Quality Control Current Good Manufacturing Practice regulations establish minimum standards for pharmaceutical quality control operations, covering facility design, equipment qualification, and testing protocols. cGMP requirements mandate that quality control laboratories maintain adequate space, equipment, and personnel to perform necessary testing without compromising accuracy or timeliness. Quality control compliance under cGMP extends beyond test execution to encompass laboratory management systems. Companies must establish written procedures covering all testing activities, train personnel on those procedures, and document adherence during actual operations. Deviation from established protocols requires investigation and justification, creating accountability that reinforces consistent practices. Regular internal audits verify that practices align with written procedures and regulatory requirements. Management review processes ensure quality control systems remain effective and adapt to changing business needs. This disciplined approach creates sustainable quality systems that withstand regulatory inspections while supporting operational excellence. 6.3 Validation and Qualification Standards Validation proves that processes, equipment, and methods consistently produce intended results under stated conditions. In pharmaceutical quality control, validation applies to analytical methods, computer systems, cleaning procedures, and numerous other activities critical to quality assurance. Rigorous validation protocols demonstrate that testing methods accurately measure intended attributes with appropriate precision, specificity, and robustness. Equipment qualification precedes validation, verifying that instruments and systems meet design specifications and operate properly before use in production or testing. This staged approach progresses from design qualification through installation, operational, and performance qualification phases, building evidence that equipment functions as intended. The depth and frequency of validation and qualification activities follows risk-based principles, with more critical applications receiving enhanced scrutiny. Revalidation schedules ensure that changes in equipment, materials, or procedures don’t compromise previously demonstrated capabilities. 7. Quality Systems and Process Management 7.1 Standard Operating Procedures (SOPs) Development Standard operating procedures provide the foundation for consistent pharmaceutical quality control operations by documenting exactly how activities should be performed. Well-written SOPs balance sufficient detail to ensure reproducibility with clarity that prevents confusion. These documents specify everything from sample handling requirements to instrument operation sequences. Developing effective SOPs requires input from personnel who actually perform the work, ensuring procedures reflect operational reality. Draft procedures undergo review by quality assurance, subject matter experts, and management before approval. This collaborative development process builds ownership while catching potential issues. SOP management extends beyond initial writing to encompass version control, change management, and periodic review ensuring continued relevance. Training programs ensure personnel understand current procedures and can execute them properly. 7.2 Deviation Management and CAPA Systems Deviations from established procedures or specifications demand immediate attention and thorough investigation in pharmaceutical quality control. When test results fall outside acceptance criteria or personnel fail to follow protocols, deviation management systems capture details, assign responsibility for investigation, and track resolution. Corrective and preventive action systems address root causes rather than just treating symptoms of quality problems. CAPA investigations dig deeper than immediate circumstances to identify underlying issues enabling deviations. Effective corrective actions eliminate root causes, preventing recurrence of similar problems. The effectiveness of deviation and CAPA systems depends on rigorous follow-through and verification of action effectiveness. Pharmaceutical companies track metrics like deviation frequency, investigation timeliness, and CAPA recurrence rates. These indicators reveal system health and identify opportunities for improvement. 7.3 Change Control in Quality Control Operations Change control processes manage modifications to pharmaceutical quality control operations, ensuring changes don’t inadvertently compromise quality or compliance. Whether adjusting analytical methods, upgrading laboratory equipment, or revising testing schedules, formal change control evaluates potential impacts before implementation. Effective change control balances thorough evaluation with operational agility. Risk-based approaches focus scrutiny on changes with significant quality implications while streamlining approval for low-risk modifications. Change proposals undergo review by quality assurance, technical experts, and affected departments. Documentation and communication form critical change control elements, ensuring all stakeholders understand modifications and their implications. Post-implementation review verifies that changes achieved intended benefits without creating new problems. 8. Common Challenges and Practical Solutions 8.1 Addressing Sample Testing Backlogs Sample testing backlogs create cascading problems throughout pharmaceutical operations, delaying batch release and straining supply chains. These backlogs typically stem from insufficient capacity relative to testing demand, whether due to equipment limitations, staffing constraints, or inefficient workflows. Strategic capacity planning provides the foundation for addressing testing backlogs sustainably. Pharmaceutical companies analyze testing demand patterns, considering seasonal variations, new product launches, and process changes affecting sample loads. This forward-looking approach enables proactive resource allocation, whether through equipment additions, staffing adjustments, or workflow optimization. A mid-size pharmaceutical manufacturer tackled persistent backlogs by implementing risk-based testing protocols combined with automation. The company focused intensive testing on 15% of high-risk products while streamlining protocols for products with three or more years of consistent performance. Combined with automated sample preparation systems, this approach reduced testing time by 30% while maintaining quality standards. The key was balancing regulatory requirements with operational efficiency, conducting thorough risk assessments to justify reduced testing frequency for lower-risk products. Process optimization and technology adoption accelerate existing operations without proportional resource increases. Automated sample preparation systems, high-throughput analytical methods, and streamlined documentation workflows improve laboratory productivity significantly. These improvements reduce per-sample processing time, enabling laboratories to handle greater testing volumes with existing resources. 8.2 Managing Out-of-Specification (OOS) Results Out-of-specification results represent one of the most challenging situations in pharmaceutical quality control, requiring thorough investigation while maintaining objectivity and scientific rigor. When test results fall outside acceptance criteria, immediate notification triggers investigation protocols examining laboratory practices, instrument performance, and potential product quality issues. Effective OOS investigations follow structured approaches beginning with laboratory investigation phases examining testing process integrity. This initial phase evaluates whether laboratory errors could explain unexpected results, examining everything from sample handling to instrument calibration. Only after confirming testing accuracy do investigations expand to process-related causes. Prevention strategies prove more effective than reactive investigation alone. Regular method suitability assessments verify that analytical procedures remain appropriate for their intended use. Preventive maintenance programs keep instruments operating within specifications, reducing test failures from equipment issues. Personnel training reinforces proper techniques and the importance of following protocols precisely. 8.3 Balancing Speed with Thoroughness Pharmaceutical quality control faces constant tension between accelerating testing timelines and maintaining thoroughness necessary for reliable results. Business pressures demand rapid batch release supporting just-in-time manufacturing and responsive supply chains, while quality imperatives require comprehensive testing confirming all specifications are met. Risk-based testing strategies optimize resource allocation by focusing intensive testing where it matters most. Products with extensive performance history and demonstrated process control may justify streamlined testing protocols, while new products or processes undergoing changes warrant enhanced scrutiny. Technology adoption and process improvement initiatives accelerate testing without compromising quality. Parallel testing approaches, where multiple analyses run simultaneously rather than sequentially, significantly reduce total testing time. Advanced analytical methods providing faster results with equal or better accuracy replace traditional lengthy procedures. Laboratory automation eliminates manual handling steps that consume time without adding value. 8.4 Supporting Digital Transformation in Pharmaceutical Quality Control Modernizing pharmaceutical quality control requires a combination of domain expertise, technology capabilities, and a deep understanding of regulatory expectations. Organizations increasingly seek support in implementing validated systems, integrating data across platforms, and automating critical processes. This includes areas such as computer systems validation, system integration, qualification and validation activities, as well as audit preparation and cybersecurity. By aligning technology with quality processes, companies can improve efficiency, enhance compliance, and build scalable quality control environments ready for future challenges. A structured and well-executed digital transformation strategy enables pharmaceutical organizations to move from reactive quality control toward proactive, data-driven quality assurance. 9. Future-Proofing Your Quality Control Operations The pharmaceutical industry’s trajectory toward increased complexity and regulatory scrutiny demands quality control operations that anticipate future requirements. Future-proofing begins with digital transformation initiatives that integrate quality control data with broader manufacturing and business intelligence systems, enabling advanced analytics and predictive modeling that improves quality while enhancing efficiency. Continuous improvement cultures separate organizations that merely maintain compliance from those achieving quality excellence. Structured improvement methodologies like Lean and Six Sigma provide frameworks for systematic problem-solving and sustainable change, creating organizations that adapt readily to new challenges. Investing in personnel development ensures organizations possess capabilities needed for emerging quality control approaches. Training programs covering advanced analytical techniques, data analysis skills, and regulatory knowledge prepare quality control professionals for evolving roles. As routine tasks become automated, human expertise focuses increasingly on complex problem-solving, strategic thinking, and scientific judgment. Quality control operations must evolve from isolated functional departments to integrated elements of holistic quality management systems. Breaking down silos between quality control, quality assurance, manufacturing, and other functions creates organizations where quality responsibility is shared. Cross-functional collaboration improves problem-solving, accelerates improvement initiatives, and builds company-wide commitment to quality. Full disclosure: TTMS provides technology support for pharmaceutical companies modernizing quality-related operations. This includes system integration, process automation, business intelligence, cloud-based platforms, cybersecurity, and support for validated digital environments. Through business intelligence tools, process automation solutions, and Azure-based cloud platforms, companies can achieve the data integration and analytical capabilities essential for modern pharmaceutical quality control. These technology foundations support real-time visibility and informed decision-making that transform quality control from reactive testing to proactive quality assurance. When evaluating technology partners, companies should assess implementation experience, validation support capabilities, and ongoing maintenance commitments. The path forward balances technological innovation with fundamental quality principles that have always protected patient safety. Advanced analytics and automation enhance efficiency and expand capabilities, but they supplement rather than replace scientific rigor and quality culture. Organizations that successfully integrate new capabilities while maintaining core quality commitments will define excellence in pharmaceutical manufacturing for years to come, delivering products meeting the highest standards that patients deserve and regulations demand. 10. How TTMS helps pharmaceutical companies maintain compliant quality control environments Modern pharmaceutical quality control depends not only on laboratory procedures and testing standards, but also on properly qualified systems, validated environments, and reliable compliance processes. As regulatory expectations continue to evolve, pharmaceutical companies need partners who understand both technology and regulated quality operations. TTMS Quality Management Services supports pharmaceutical organizations in building and maintaining compliant quality control environments aligned with GMP and GxP requirements. This includes support for qualification and validation activities, computer systems validation (CSV), audit readiness, data integrity initiatives, and quality process optimization. Through TTMS Qualification and Validation Services, companies can improve control over regulated systems and infrastructure while ensuring that critical processes, equipment, and digital platforms operate consistently and in accordance with regulatory expectations. TTMS also supports pharmaceutical companies in maintaining lifecycle compliance across laboratory systems, manufacturing environments, and quality management processes. This helps organizations improve inspection readiness, strengthen operational reliability, and reduce compliance risks across regulated environments. 11. Key Takeaways for Pharmaceutical Quality Control in 2026 Pharmaceutical quality control is evolving from reactive end-product testing toward proactive, data-driven quality assurance supported by validated digital systems. Modern pharmaceutical environments increasingly rely on integrated platforms such as LIMS, QMS, MES, and ERP systems to improve traceability, audit readiness, and operational visibility. Regulatory expectations continue to emphasize data integrity, electronic records, cybersecurity, and lifecycle validation under frameworks such as 21 CFR Part 11, EU Annex 11, and risk-based CSA approaches. AI and automation technologies can improve efficiency in areas such as inspection, environmental monitoring, documentation workflows, and deviation management, but they require careful validation, governance, and ongoing monitoring. Pharmaceutical companies modernizing quality operations should focus not only on compliance, but also on interoperability, system integration, and scalable digital infrastructure that supports long-term operational resilience. Successful quality control strategies in 2026 balance technological innovation with scientific rigor, regulatory compliance, and patient safety. 12. Frequently Asked Questions About Pharmaceutical Quality Control What is pharmaceutical quality control and why is it important? Pharmaceutical quality control is a structured process that ensures every drug product meets defined standards of safety, efficacy, and purity before it reaches patients. It covers testing of raw materials, monitoring of manufacturing processes, and verification of finished products. Its importance lies in protecting patient health and maintaining regulatory compliance. Without effective quality control, even small deviations can lead to serious risks, including product recalls, regulatory penalties, and damage to company reputation. In modern pharmaceutical environments, quality control also supports operational efficiency by identifying issues early and reducing waste. What is the difference between quality control and quality assurance in pharma? Quality control focuses on testing and verifying products, while quality assurance is a broader system that ensures processes are designed and managed correctly. In practice, quality control checks whether a product meets specifications, whereas quality assurance ensures that the entire system consistently produces compliant results. Quality assurance includes procedures, audits, validation, and risk management, while quality control operates within this framework as a key operational component. Both are essential and closely connected, but they serve different roles within the pharmaceutical quality system. What systems are used in pharmaceutical quality control? Pharmaceutical quality control relies on several interconnected digital systems that support data collection, analysis, and compliance. These include Laboratory Information Management Systems for managing laboratory data, Quality Management Systems for handling deviations, CAPA, and documentation, and Manufacturing Execution Systems for monitoring production processes. These systems must work together to ensure full traceability and data integrity. Proper integration between them is critical, as fragmented systems can lead to delays, errors, and compliance risks. What is computer systems validation in pharmaceutical quality control? Computer systems validation is the process of ensuring that digital systems used in pharmaceutical operations function correctly, consistently, and in compliance with regulatory requirements. It covers the entire system lifecycle, from design and implementation to maintenance and updates. Validation ensures that systems such as LIMS or QMS produce reliable data, maintain audit trails, and protect data integrity. It is a key requirement under regulations such as 21 CFR Part 11 and EU Annex 11, and it plays a central role in modern quality control environments. How do pharmaceutical companies prepare for regulatory audits? Preparing for regulatory audits requires ongoing effort rather than last-minute actions. Companies must maintain accurate and up to date documentation, ensure full traceability of data, and regularly review their processes for compliance gaps. Internal audits and mock inspections help identify weaknesses before official inspections take place. It is also important that employees understand procedures and can demonstrate them during audits. A well prepared organization is able to quickly provide evidence of control over processes, systems, and data, which significantly reduces the risk of audit findings. Why is data integrity critical in pharmaceutical quality control? Data integrity ensures that all information generated during pharmaceutical processes is accurate, complete, and reliable. This is essential because decisions about product quality are based entirely on this data. If data is incomplete, altered, or not traceable, it undermines trust in the entire quality system. Regulatory authorities place strong emphasis on data integrity, and failures in this area are a common reason for warning letters. Maintaining strong data integrity requires both technical controls and a culture of accountability within the organization. How is automation changing pharmaceutical quality control? Automation is transforming pharmaceutical quality control by reducing manual work, increasing consistency, and accelerating testing processes. Automated systems can handle repetitive tasks such as sample preparation, data entry, and inspection with greater accuracy than manual operations. This reduces the risk of human error and improves overall efficiency. At the same time, automation enables faster data processing and real time monitoring, allowing companies to detect issues earlier and respond more effectively. However, automated systems must be properly validated and integrated to ensure compliance. What role does cybersecurity play in pharmaceutical quality systems? Cybersecurity has become a critical element of pharmaceutical quality systems due to the increasing reliance on digital platforms. Quality control systems store sensitive data that must be protected from unauthorized access, loss, or manipulation. Effective cybersecurity measures include access control, data encryption, system monitoring, and regular risk assessments. These measures help ensure that data remains secure and trustworthy, which is essential for both regulatory compliance and business continuity. As digital transformation accelerates, cybersecurity is no longer optional but a fundamental requirement.
ReadGPT-5.5 for Business: A New Era of AI Agents
Most AI tools still answer questions. GPT-5.5 starts finishing the job. This release is less about smarter responses and more about execution. GPT-5.5 is built for multi-step work across code, documents, data, and business systems – where understanding intent, using tools, and completing workflows matter more than generating text. For companies already experimenting with AI agents, automation, and enterprise copilots, this shift is critical. The question is no longer “Can AI help?” but “How much of the process can it handle on its own?” 1. Why GPT-5.5 for Business Is More Than a New Model Name AI model launches often look similar from the outside. A new version appears, benchmark numbers go up, early users post enthusiastic screenshots, and companies wonder whether they should update their AI roadmap. GPT-5.5 deserves a more careful business reading because its core value is not just “better answers.” It is better task completion. For business users, this matters because most real work is not a single prompt. A finance analyst does not only need a summary. They may need to review hundreds of documents, identify exceptions, build a model, explain assumptions, and prepare a report. A software team does not only need a code snippet. It may need an agent that understands an existing codebase, creates a plan, edits multiple files, runs tests, fixes regressions, and documents the change. A customer service operation does not only need a nice response. It needs an assistant that can understand policy, retrieve the right information, call tools, escalate edge cases, and maintain consistency. GPT-5.5 is aimed at exactly this category of work. OpenAI positions it as a model for complex professional tasks, especially coding, agentic workflows, knowledge work, computer use, and early scientific research. That makes it especially relevant for companies thinking beyond “AI as a writing assistant” and toward “AI as an operating layer for business workflows.” 2. The Real Shift: From Prompting an Assistant to Delegating a Workflow The biggest difference between GPT-5.5 and earlier models is behavioral. Previous models could be impressive in short interactions, but complex business work often required heavy prompt engineering, step-by-step supervision, manual checking, and repeated correction. GPT-5.5 reduces some of that friction. It is better at understanding what outcome the user is trying to reach and at choosing a path toward that outcome. This is why the language around GPT-5.5 focuses so strongly on agents. An agent is not just a model that generates text. It is a model connected to tools, data, systems, permissions, and workflows. In that context, small improvements in reasoning, tool use, context management, and instruction following compound quickly. A slightly better tool call can prevent a broken workflow. A more persistent reasoning loop can reduce human hand-holding. Better context retention can keep a long-running task aligned with business requirements. For companies, this changes the adoption conversation. Instead of asking only “Can AI write a better answer?”, the more valuable question becomes “Can AI complete this process with defined guardrails, measurable quality, and human review only where it matters?” GPT-5.5 makes that question more realistic. 3. How GPT-5.5 Differs from GPT-5.4 and Earlier GPT-5 Models GPT-5.5 is best understood as a practical improvement over GPT-5.4 in sustained, multi-step work. It is not necessarily the model every business should use for every AI interaction. For simple summarization, short classification, routine extraction, or low-risk chatbot interactions, smaller and cheaper models may still be the better choice. The advantage of GPT-5.5 appears when the task is complex enough that planning, verification, tool orchestration, and long-context reasoning matter. One important difference is token efficiency. GPT-5.5 is more expensive per token than GPT-5.4, but OpenAI emphasizes that it can complete many complex Codex tasks with fewer tokens. In business terms, this means the sticker price is not the only metric. The real metric is cost per completed workflow. A model that costs more per token but needs fewer retries, fewer failed runs, and fewer manual interventions may be cheaper in production than it looks on a pricing page. Another important difference is prompting style. GPT-5.5 is less dependent on process-heavy prompt stacks. OpenAI’s guidance suggests that shorter, outcome-first prompts often work better than older prompts that over-specify every step. That is meaningful for enterprise adoption because many companies have accumulated long, fragile prompt templates to compensate for earlier model weaknesses. With GPT-5.5, teams may need to rethink those prompts rather than simply reuse them. The model also supports high reasoning effort settings in the API, including xhigh, and offers a 1M token context window in the API. In Codex, GPT-5.5 is available with a 400K context window. These numbers matter for document-heavy, code-heavy, and research-heavy workflows, although businesses should remember that a large context window is only useful when the model can use it reliably and when the system architecture retrieves the right information in the first place. 4. What GPT-5.5 Was Trained On – And What OpenAI Does Not Fully Disclose OpenAI has not published a full dataset inventory for GPT-5.5, and businesses should be cautious with any claims about its exact training data, model size, or architecture. Public information remains intentionally high-level. According to OpenAI’s system card, GPT-5.5 was trained on a mix of publicly available data, licensed or partner-provided content, and data generated or reviewed by humans. The training pipeline includes filtering to improve quality, reduce risks, and limit exposure to personal data. A key differentiator is post-training through reinforcement learning, which improves reasoning. In practice, this means the model is better at planning, testing different approaches, recognizing mistakes, and aligning with policies and safety expectations. For business users, the takeaway is clear: GPT-5.5 is not valuable because it “knows everything,” but because it is better at working through complex tasks. However, it should not replace enterprise data architecture. To deliver real value, it must be integrated with governed data sources, retrieval systems, permission-aware tools, logging, and human review. If you want a deeper look at how earlier GPT models were trained and how their data sources evolved over time, see our article on GPT-5 training data evolution. 5. Where Businesses May Feel the GPT-5.5 “Wow Effect” The “wow effect” of GPT-5.5 is not necessarily a single spectacular answer. It is the feeling that a model can take a messy, multi-part business request and move it toward completion with less supervision than before. 5.1 Agentic coding and software development Software engineering is one of the strongest areas for GPT-5.5. The model performs well on coding and terminal-based benchmarks, but the more interesting business point is how it behaves inside development workflows. It can help with implementation, refactoring, debugging, test generation, codebase understanding, and validation. For development teams, this is less about replacing engineers and more about compressing parts of the software delivery lifecycle. The value is especially visible in large, existing codebases where a model must understand context, respect architecture, predict what may break, and adjust surrounding files. Earlier models could generate impressive code in isolation. GPT-5.5 is more useful when the work involves maintaining consistency across a system. 5.2 Knowledge work and document-heavy workflows GPT-5.5 is also positioned for broader knowledge work: analyzing information, creating documents and spreadsheets, synthesizing research, and moving across tools. This makes it relevant for teams in finance, consulting, legal operations, HR, sales operations, procurement, and compliance. Examples from early use show the model being applied to document review, operational research, business reporting, and structured decision workflows. The important pattern is not a specific use case, but a class of work: repetitive yet cognitively demanding tasks where humans still need quality, judgment, and accountability, but where much of the gathering, structuring, cross-checking, and drafting can be accelerated. 5.3 Scientific and technical research GPT-5.5 also shows stronger performance in scientific and technical workflows. These workflows require more than answering a difficult question. They involve exploring hypotheses, analyzing datasets, interpreting results, checking assumptions, and turning partial evidence into a useful next step. For R&D-driven companies, life sciences, advanced manufacturing, energy, engineering, and data-intensive industries, this points to an important future direction. AI will increasingly act as a research partner that helps experts move faster through analysis loops. However, in high-stakes research environments, validation remains essential. A model can accelerate expert work, but it cannot replace domain accountability. 6. GPT-5.5 vs Competitors: Claude, Gemini, DeepSeek, and the New AI Stack The competitive landscape around GPT-5.5 is not simple because the best model depends on the workflow. GPT-5.5 competes most directly with Claude Opus 4.7 and Gemini 3.1 Pro in the frontier model category, while open-weight and lower-cost models from companies such as DeepSeek, Mistral, Qwen, and others continue to pressure the market from the cost and deployment-control side. Claude Opus 4.7 remains a serious competitor for complex coding, long-running reasoning, and professional knowledge work. Anthropic emphasizes reliability, instruction following, long-context performance, and data discipline. In practice, many teams will compare GPT-5.5 and Claude not only as models, but as ecosystems: OpenAI with ChatGPT, Codex, Responses API, hosted tools, and enterprise channels; Anthropic with Claude, Claude Code, and its own enterprise integrations. Gemini 3.1 Pro is another major competitor, especially for multimodal reasoning, creative technical prototyping, visual inputs, audio, video, PDFs, and Google ecosystem workflows. It is strong where businesses need AI to understand different media types and build interactive or visual outputs. GPT-5.5 appears particularly strong in agentic coding, tool-heavy workflows, and OpenAI-native execution environments, while Gemini may be attractive for teams already deeply invested in Google platforms or multimodal product experiences. Open-weight and lower-cost models create a different kind of competition. They may not always match GPT-5.5 in frontier agentic performance, but they can be attractive for cost-sensitive workloads, self-hosting, regional compliance, customization, and vendor diversification. For many enterprises, the future will not be one model. It will be a portfolio: frontier models for complex orchestration, smaller models for routine tasks, and specialized models for domain-specific workloads. That is why the real question is not “Is GPT-5.5 the best model?” A better question is “Where does GPT-5.5 create enough workflow value to justify its cost, integration effort, and governance requirements?” 7. GPT-5.5 Availability: Who Can Use It? GPT-5.5 is available across several surfaces, but access depends on the product and plan. In ChatGPT, GPT-5.5 Thinking is available for Plus, Pro, Business, and Enterprise users. GPT-5.5 Pro, designed for harder questions and higher-accuracy work, is available for Pro, Business, and Enterprise users. In Codex, GPT-5.5 is available for Plus, Pro, Business, Enterprise, Edu, and Go plans, with a 400K context window. This matters for software teams because Codex is one of the most natural environments for GPT-5.5’s agentic coding capabilities. For developers, GPT-5.5 is available through the API with a 1M context window, text and image input, and text output. It supports reasoning effort settings and the tool capabilities expected from current OpenAI production workflows. GPT-5.5 Pro is also positioned for higher-accuracy work at a significantly higher price point. For enterprises, availability is expanding beyond the OpenAI platform itself. GPT-5.5 is also appearing in enterprise cloud channels such as Microsoft Foundry and Amazon Bedrock. This matters because many organizations want to deploy AI inside existing cloud governance, procurement, identity, security, and compliance structures. For large companies, the model is only one part of the decision. The deployment channel can be just as important. 8. Business Use Cases Where GPT-5.5 Fits Best GPT-5.5 is not the right answer for every AI problem. It is strongest where work is complex, multi-step, tool-driven, and expensive when done manually. 8.1 AI agents for internal operations GPT-5.5 can serve as the reasoning layer for agents that handle internal workflows: routing requests, preparing reports, checking documents, updating systems, generating follow-ups, and escalating exceptions. The business value comes from reducing coordination costs and giving employees a more capable interface for operational work. 8.2 Software development and modernization Development teams can use GPT-5.5 to accelerate refactoring, test generation, debugging, documentation, migration planning, and feature implementation. It may be particularly useful in modernization projects where companies need to understand and change complex legacy systems. 8.3 Data engineering and analytics workflows For data teams, GPT-5.5 can help transform ambiguous business questions into analysis plans, generate SQL or Python, inspect data quality issues, explain anomalies, and draft business-ready summaries. It should not replace data governance, but it can make analytics workflows faster and more accessible. 8.4 Customer service and support automation GPT-5.5 can improve support agents that must retrieve information, follow policy, call systems, and complete service workflows. Its strength in multi-step reasoning and tool use is relevant for cases that go beyond simple FAQ automation. 8.5 Research, compliance, and document review Document-heavy teams can use GPT-5.5 for first-pass analysis, extraction, comparison, summarization, risk flagging, and report generation. In regulated environments, human review and audit trails remain essential, but the model can reduce time spent on repetitive reading and structuring. 9. Business Risks and Limitations: Where GPT-5.5 Still Needs Governance GPT-5.5 is stronger, but it is still a probabilistic AI system. It can still make mistakes, misunderstand ambiguous instructions, select the wrong tool, overstate confidence, or produce outputs that require verification. Businesses should resist the temptation to turn benchmark performance into blind trust. Cost is another practical limitation. GPT-5.5 is more expensive per token than GPT-5.4. The business case depends on whether it reduces total workflow cost through fewer retries, fewer manual interventions, better completion rates, and higher-quality outputs. That requires measurement, not assumptions. Cybersecurity is also a special area. GPT-5.5 has stronger cyber capabilities than previous models, which is valuable for defenders but also creates misuse risk. OpenAI has added stricter safeguards and trusted-access approaches for certain cyber workflows. Enterprises should treat this as a reminder that powerful agents need policy, monitoring, access control, and review layers. There is also a migration risk. GPT-5.5 should not be treated as a drop-in replacement for older prompt stacks. Because it can work better with shorter, outcome-first prompts, organizations may need to re-evaluate their existing instructions, tools, evaluation sets, and failure handling. A careless migration may hide the model’s benefits or introduce new issues. 10. How to Evaluate GPT-5.5 Before a Production Rollout The best way to evaluate GPT-5.5 is not to ask whether it is impressive. It is to test whether it improves a specific business workflow. Start by selecting a set of representative tasks: a real support workflow, a real code refactor, a real document review process, a real reporting cycle, or a real data analysis request. Define what success means before running the model. Success may include accuracy, completion rate, time saved, number of human corrections, cost per completed task, escalation quality, user satisfaction, or reduction in repeated work. Then compare GPT-5.5 with your current model stack. Include GPT-5.4 or other lower-cost models, and consider competitors such as Claude or Gemini if they are relevant to your environment. The goal is not to crown a universal winner. The goal is to decide which model should handle which class of task. For production systems, combine GPT-5.5 with structured logging, evaluation datasets, permission-aware tools, retrieval quality checks, human-in-the-loop checkpoints, and rollback options. The more autonomy you give an AI agent, the more important system design becomes. 11. What GPT-5.5 Means for Business Strategy GPT-5.5 signals a shift in enterprise AI: the advantage is no longer access to a model, but the ability to redesign workflows around AI execution. Many companies can use a chatbot. Far fewer can safely integrate AI agents into software delivery, operations, finance, and data processes. This makes AI a strategic capability. GPT-5.5 enables systems that not only assist, but coordinate work across tools and teams. The real value comes from combining model capabilities with process design, data engineering, architecture, security, and change management. For business leaders, the priority is clear: treat GPT-5.5 as part of your operating model. Identify workflows ready for automation, define where human oversight is required, connect the right data sources and systems, and measure outcomes. At TTMS, we help organizations turn these priorities into production-ready solutions – from AI consulting and agent design to software development, automation, and data engineering. If you are planning to implement GPT-5.5 or AI agents in your organization, contact us to design and deploy the right solution for your business. FAQ: GPT-5.5 for Business Is GPT-5.5 worth adopting for business? GPT-5.5 is worth evaluating if your company works with complex, multi-step, tool-heavy workflows. It is especially relevant for software development, AI agents, research, document-heavy operations, analytics, and business automation. However, it may not be necessary for every task. For simple summarization, classification, or short Q&A, a smaller and cheaper model may be enough. The best approach is to test GPT-5.5 against real workflows and measure cost per completed outcome, not just cost per token. How is GPT-5.5 different from GPT-5.4? GPT-5.5 improves on GPT-5.4 mainly in sustained professional work. It is better at understanding intent, using tools, maintaining context, checking its work, and completing multi-step tasks with less manual guidance. It is also designed to be more token-efficient in complex workflows, although its per-token API pricing is higher. For businesses, the difference is most visible in agentic coding, workflow automation, data analysis, and document-heavy work. If your current AI use case is simple, the improvement may be less dramatic. Can GPT-5.5 replace developers, analysts, or business specialists? GPT-5.5 should be seen as an accelerator rather than a full replacement for expert roles. It can help developers write, refactor, test, and debug code faster. It can help analysts structure research, generate queries, inspect data, and draft reports. It can help business teams automate repetitive knowledge work. But it still needs clear requirements, high-quality data, tool access, validation, and human accountability. The strongest use cases are usually human-plus-AI workflows where experts focus on judgment, architecture, review, and decisions. Is GPT-5.5 safe for enterprise data? Enterprise safety depends on how GPT-5.5 is deployed, not only on the model itself. Companies should consider data retention, access control, user permissions, logging, compliance requirements, and the deployment channel they choose. API, ChatGPT Business, ChatGPT Enterprise, Microsoft Foundry, and AWS Bedrock may all have different governance implications. For sensitive workflows, businesses should use permission-aware integrations, avoid unnecessary data exposure, and add human review for high-impact decisions. The model can be part of a secure system, but it is not a security architecture by itself. Should companies choose GPT-5.5, Claude Opus, Gemini, or an open-weight model? There is no universal answer because each model family has different strengths. GPT-5.5 is a strong choice for OpenAI-native agentic workflows, Codex, complex coding, tool-heavy automation, and enterprise deployments connected to the OpenAI ecosystem. Claude Opus remains highly competitive for long-running reasoning, coding, and disciplined professional work. Gemini is attractive for multimodal workflows and companies invested in the Google ecosystem. Open-weight models may be preferable for cost control, customization, or self-hosting. Many mature companies will use several models and route tasks based on complexity, cost, latency, risk, and governance requirements.
ReadThe world’s largest corporations have trusted us
We hereby declare that Transition Technologies MS provides IT services on time, with high quality and in accordance with the signed agreement. We recommend TTMS as a trustworthy and reliable provider of Salesforce IT services.
TTMS has really helped us thorough the years in the field of configuration and management of protection relays with the use of various technologies. I do confirm, that the services provided by TTMS are implemented in a timely manner, in accordance with the agreement and duly.
Ready to take your business to the next level?
Let’s talk about how TTMS can help.

Michael Foote
Business Leader & CO – TTMS UK